GitHub Actions Workflow Scanner: Pwn-Request Detection
This scanner, available as part of JFrog Advanced Security, detects the "Pwn-Request" vulnerability in GitHub Actions workflows.
What Is a Pwn-Request?
A GitHub workflow that runs on pull_request_target and checks out the pull request code may be vulnerable to GitHub Actions code injection. An attacker can open a pull request from a forked repository and include malicious code that executes within the workflow's context. Depending on the workflow's permissions and environment, the attacker's code may perform unauthorized or harmful actions.
What Is the Risk?
An attacker may exploit the workflow to access sensitive data available in the workflow's environment, such as API keys or other secrets. Additionally, if the workflow has write permissions to the repository, the attacker may be able to modify the project by pushing malicious code.
What Are The Conditions for a Vulnerable Workflow?
This attack pattern requires two conditions to be present simultaneously in a workflow definition:
- The workflow uses the
pull_request_targettrigger (which runs with the target repo's privileges). - The workflow checks out the PR's head code (untrusted, attacker-controlled code) and runs it in that privileged context.
How Does the Scanner Work?
The scanner performs static analysis on GitHub Actions workflow YAML files and flags a vulnerable configuration (all must be true to flag):
-
The workflow YAML has a
pull_request_targettrigger. -
A step using
actions/checkoutsets itsrefto the PR head (github.event.pull_request.head.sha,github.head_ref, orrefs/pull/.../merge), meaning untrusted code from the PR fork would get checked out at runtime. -
No known mitigation is in place (any one of these marks the workflow as safe):
- Fork restriction: The workflow definition contains a condition that would prevent execution when the PR originates from a fork, either at the workflow level or on every job. This makes the checkout safe since an attacker cannot submit code from a fork.
- Trusted actor restriction: The workflow definition contains a condition that would restrict execution to trusted bots (like dependabot or renovate), either at the workflow level or on every job. Such bots are considered safe, so checking out code from their pull requests should not trigger an alert.
How To Use the Scanner?
The scanner analyzes GitHub Actions workflow YAML files only where they are located within a Docker image. It scans files matching .github/workflows/*.yml or .yaml. To trigger the scanner, scan a Docker image that contains a workflow YAML file in this path.
Here’s an example of the scanner’s output:
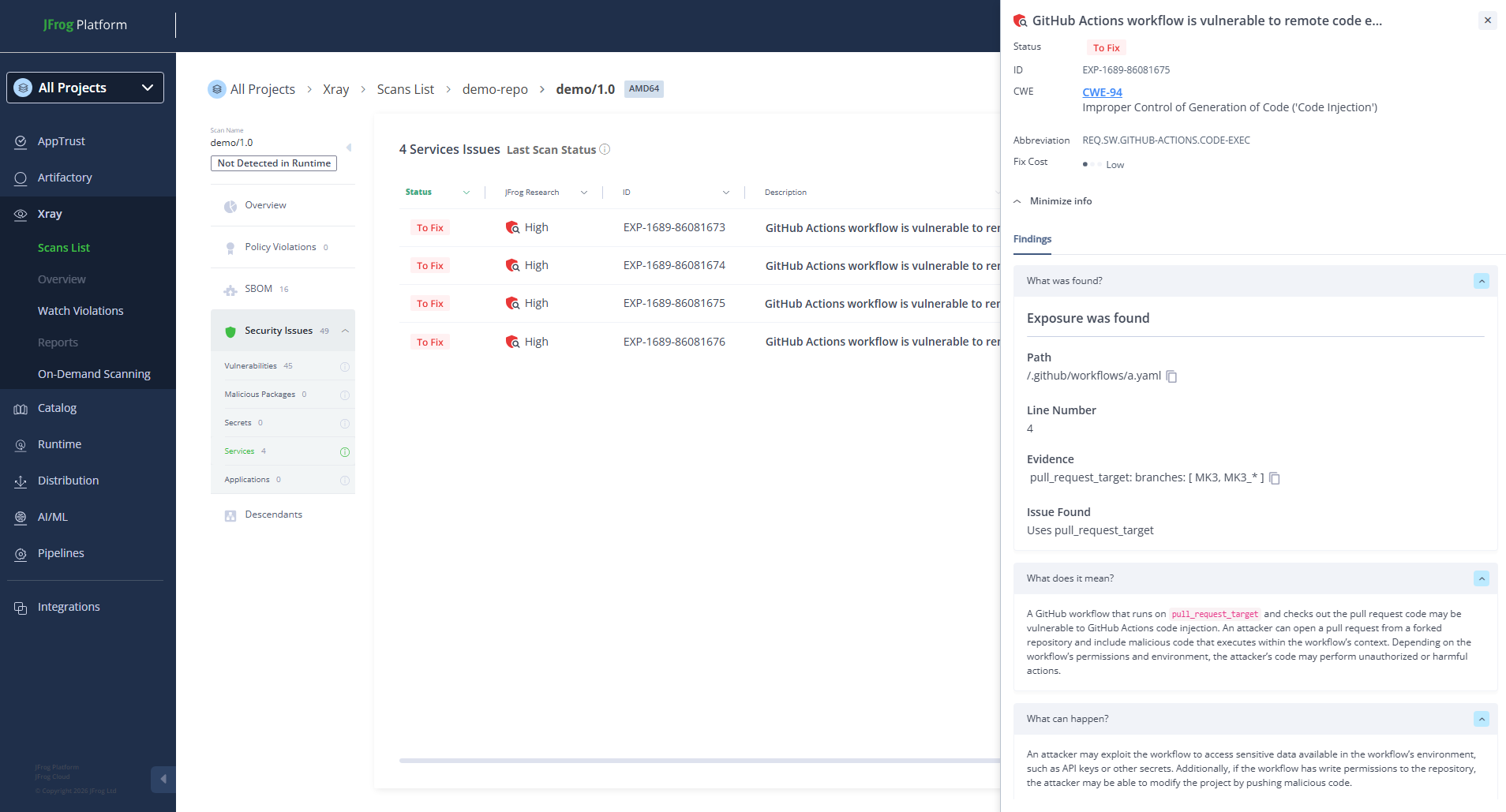
Xray Scan Results for a Vulnerable GitHub Actions Workflow
Updated about 1 month ago

