Xray Overview Page
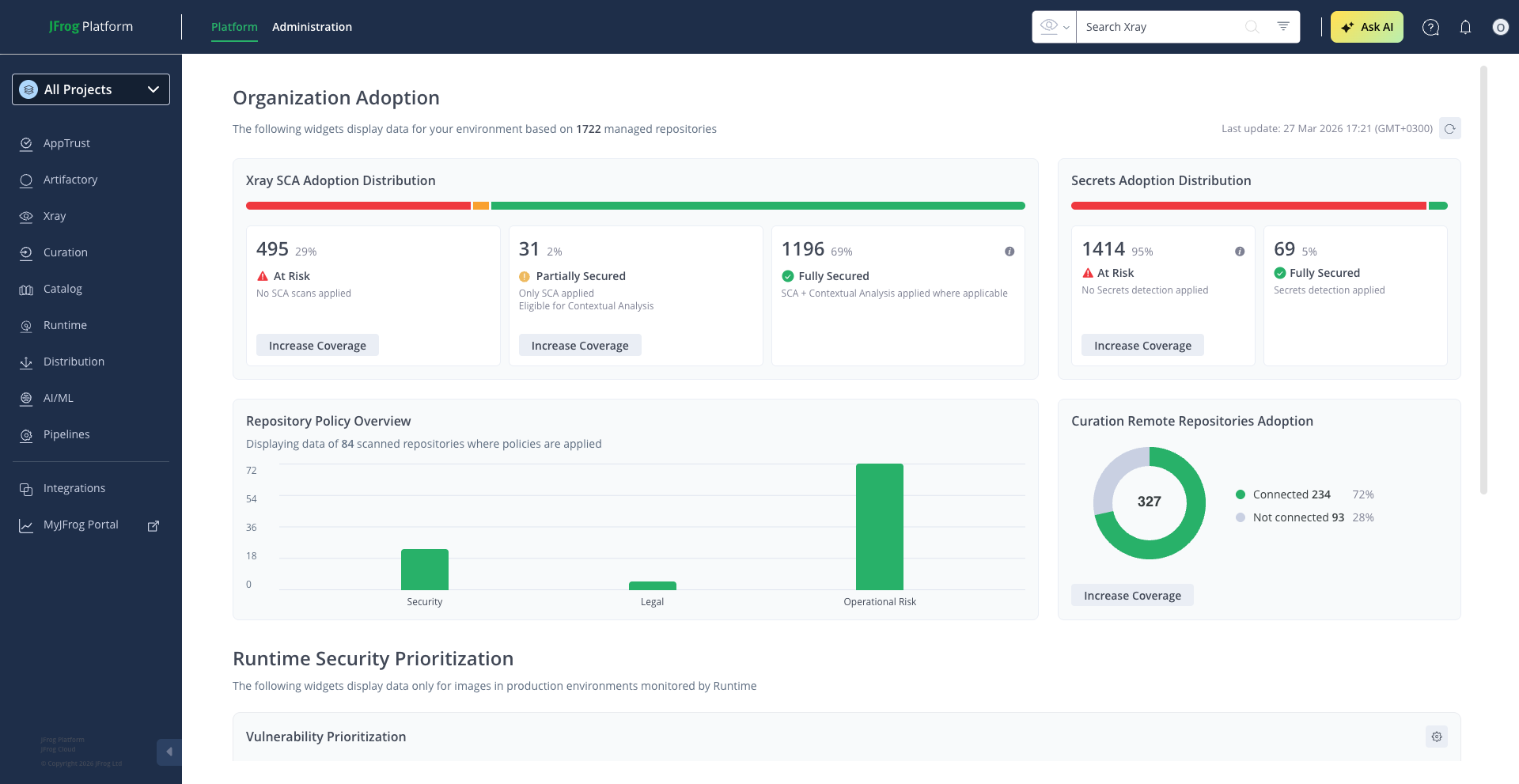
A single-pane-of-glass view of your organization's security scanning coverage, secrets detection adoption, supply chain protection, and policy enforcement.
The JFrog Platform manages repositories across many teams, technologies, and stages of the software supply chain. As that footprint grows, so does a fundamental question for anyone responsible for security: How well are we actually protected?
The Xray Overview page answers that question. Navigate to Xray > Overview to reach it.
Understanding Your Organization's Security Adoption
The Organization Adoption section of the Overview page is designed for the people who own security adoption across the organization — security champions, DevSecOps leads, and platform administrators. Rather than digging through individual repository settings or scanning logs, you get a single consolidated view of where your organization stands in terms of scanning coverage, secrets protection, supply chain defense, and policy enforcement.
The value is straightforward: you can see your coverage gaps at a glance, understand where your teams have adopted security capabilities and where they haven't, and take action directly from the dashboard to close those gaps. Every insight on this page links to the configuration needed to act on it.
Scanning and Detection Coverage
The most fundamental measure of your security posture is how many of your repositories are actually being scanned. The Overview page shows this through two complementary perspectives: vulnerability scanning and secrets detection.
For vulnerability scanning, you'll see a color-coded distribution bar that breaks your entire repository landscape into coverage levels. If your organization has JFrog Advanced Security enabled, repositories are categorized as Fully Secured (scanned for known vulnerabilities and enriched with Contextual Analysis to assess real-world exploitability), Partially Secured (scanned but not yet benefiting from Contextual Analysis), or At Risk (not indexed for scanning at all). Without Advanced Security, the view simplifies to scanned versus not scanned, with a prompt to explore what Advanced Security adds. The key insight here is not just how many repositories are scanned, but how many benefit from the deeper analysis that separates theoretical risk from practical threat.
For secrets detection, a similar distribution bar shows how many eligible repositories have secrets scanning turned on. Leaked credentials — API keys, tokens, passwords embedded in artifacts — remain one of the most common and exploitable attack vectors. This view helps you track whether your teams have enabled detection across the repositories where it matters. Hovering over the "At Risk" segment reveals whether those repositories simply haven't been configured yet or aren't eligible due to their package type, so you know exactly where to focus.
In both cases, clicking Increase Coverage takes you directly to the configuration needed to bring unprotected repositories into the fold.
Supply Chain Protection
Scanning catches problems that are already in your environment. But the stronger defense is preventing risky packages from entering in the first place.
The Overview page includes a pie chart showing how many of your remote repositories are connected to JFrog Curation versus how many are not. Connected repositories benefit from automated evaluation of open-source packages at download time — blocking malicious or risky components before they reach your developers. Repositories that aren't connected represent gaps in your supply chain perimeter.
This is a particularly important metric for organizations scaling their use of open-source software. The more remote repositories you connect to Curation, the smaller the window for risky packages to enter undetected. The Increase Coverage link takes you directly to the Curation repository settings to close those gaps.
Policy Enforcement
Detecting vulnerabilities and risks is only half the equation. The other half is enforcing standards — and the Overview page shows you how broadly that enforcement reaches.
A bar chart breaks down how many repositories are covered by each type of policy: Security policies that enforce vulnerability thresholds, Legal policies that ensure license compliance, and Operational Risk policies that flag maintenance and end-of-life concerns. A header shows the total number of repositories with at least one policy applied.
This matters because scanning without policy enforcement is passive — your teams see issues but nothing prevents risky artifacts from flowing through. Policies turn detection into governance. If no policies are applied yet, the widget prompts you to create your first one.
Keeping the View Current
The Organization Adoption section includes a Last Updated timestamp showing when the data was last computed. Click the Refresh button in the top bar to pull the latest information from across your environment.
Updated 2 months ago

