Integration Workflows
This section reviews different workflows for working with the GitHub integration with JFrog, it includes the following:
- Get Started with JFrog Artifactory and GitHub Integration
- JFrog and GitHub Integration Artifactory Administrator Workflow
- JFrog and GitHub Integration GitHub Maintainer Workflow
- JFrog and GitHub Integration Developer Workflow
Get Started with JFrog Artifactory and GitHub Integration
This section describes how to get started with JFrog Artifactory and GitHub integration.
The following diagram illustrates the participants of the respective area for the integration activity.
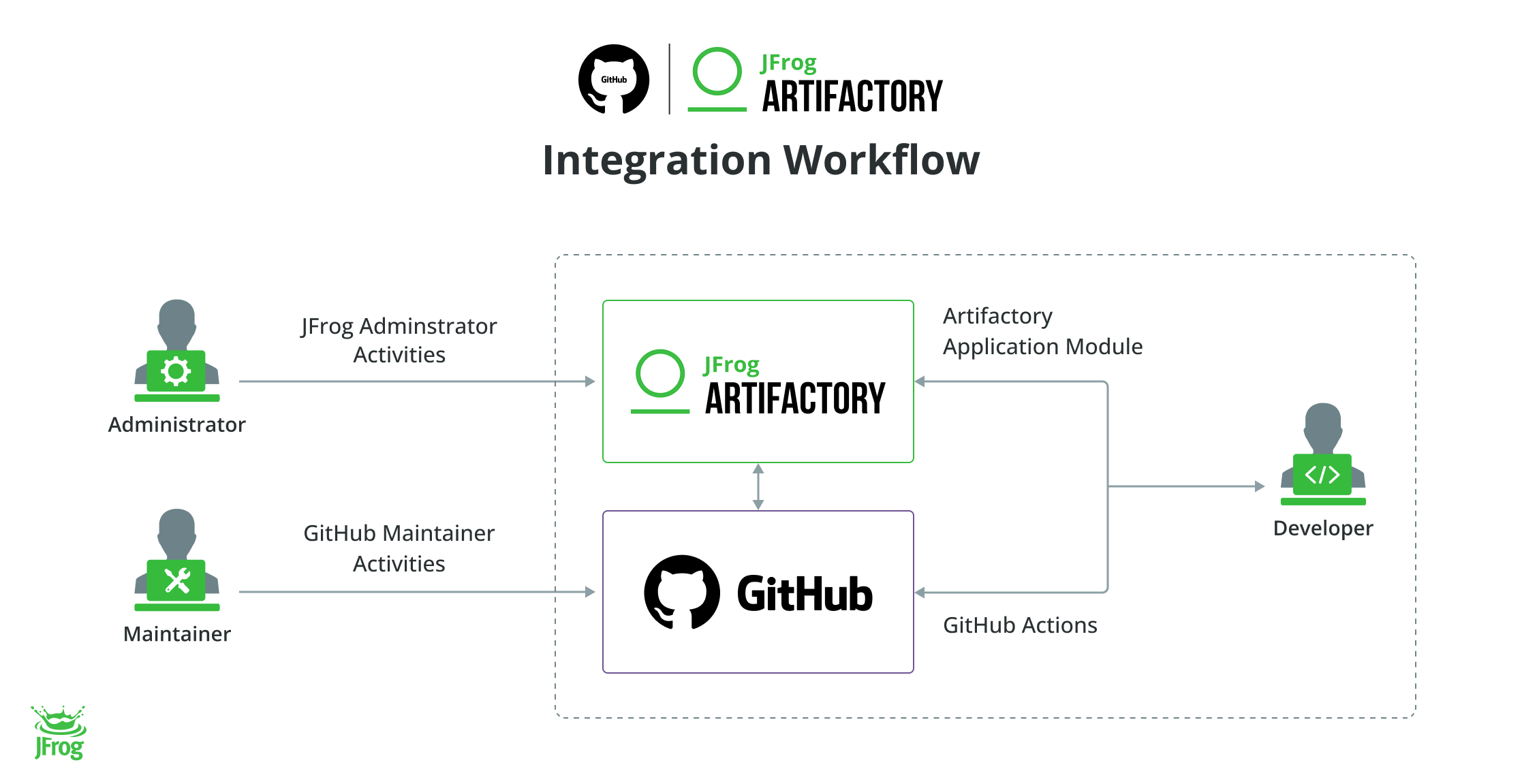
The following table describes the activities of JFrog and GitHub Integration:
Task | Description | For more information, see... | |
|---|---|---|---|
1 | JFrog Administrator Activities | Describes the steps of the JFrog Administrator Module | JFrog and GitHub Integration Artifactory Administrator Workflow |
2 | GitHub Maintainer Activities | Describes the steps of the GitHub Maintainer activities | |
3 | Developer Activities | Describes the steps of the developer activities |
JFrog App for GitHub
The JFrog GitHub App streamlines and enhances the integration between your GitHub repositories and the JFrog platform.
The Problem
- Manual Setup Is Time-Consuming: Manual configuration of OpenID Connect (OIDC) and Frogbot deployment for each repository. This not only increases the risk of errors but is also time-consuming and cumbersome for teams managing multiple repositories.
- Fragmented Security Processes: Existing security tools are fragmented, making it hard to enforce security best practices consistently across multiple repositories.
- Lack of Unified Visibility: Without a centralized view, identifying and remediating security vulnerabilities can slow down development and compliance processes.
The Solution: JFrog App for GitHub
The JFrog App for GitHub provides a comprehensive solution to these challenges, ensuring a seamless integration experience across your repositories.
Key Features
- Easy Setup: Quickly connect the JFrog App to your GitHub organization and manage all repositories from a central point.
- Centralized Authentication: Use OpenID Connect (OIDC) for a secure identity and access management system that allows for easier management.
- Automated Frogbot Deployment: Streamline the process of deploying Frogbot to scan source code for security vulnerabilities across multiple repositories automatically.
- In-Depth Security Insights: Utilize JFrog's Advanced Security to gain comprehensive visibility into vulnerabilities affecting your source code and binaries.
- Unified Dashboard: Monitor all security compliance issues directly within GitHub's Advanced Security Dashboard, simplifying visibility and management.
Advantages
- Boost Efficiency: Save time with automatic setup, reducing the need for manual adjustments.
- Enhance Security: Apply consistent security practices across repositories to protect your codebase.
- Scale with Confidence: Effortlessly onboard and secure thousands of repositories.
- Simplify Management: Resolve all security issues directly within your GitHub environment, streamlining workflows.
Get Started
Follow these steps to get started with the JFrog App for GitHub:
-
Integration With GitHub App: Install the JFrog GitHub App at the organization level or on specific repositories.
-
Configure JFrog App for GitHub
- CI integration: Enable passwordless, secure authentication for your CI/CD workflows. The CI Integration leverages OIDC to provide short-lived, scoped secrets, eliminating the need to store long-lived credentials and ensuring consistent access control across your GitHub repositories.
- Scan your Git Repositories with Frogbot: Enable seamless integration with Frogbot, which scans your pull requests and commits for security vulnerabilities and fixes them automatically.
-
Post Setup Management - JFrog OIDC Integration with GitHub: View, Add or Disconnect GitHub repositories, Edit Identity mapping. Allow JFrog and GitHub to work together to provide short-lived, scoped secrets as part of the OIDC integration. Granting "All Repositories" access is recommended to allow automatic creation of OIDC integrations for GitHub repositories.
JFrog for GitHub Dependabot
GitHub Dependabot is a tool for identifying vulnerabilities in source code dependencies, but it can often generate a high volume of security alerts, making it challenging for developers to prioritize fixes. The JFrog integration with GitHub Dependabot is designed to solve this problem by cutting through the noise, analyzing each vulnerability's context and exploitability, and helping you focus on what truly matters.
Prerequisite
- Configure JFrog OIDC Integration with GitHub App
- Add repositories to the JFrog Integration with GitHub
Work with Dependabot
Activate GitHub Dependabot
Activate Dependabot to add GitHub Organizations and prioritize alerts on GitHub Security dashboards.
-
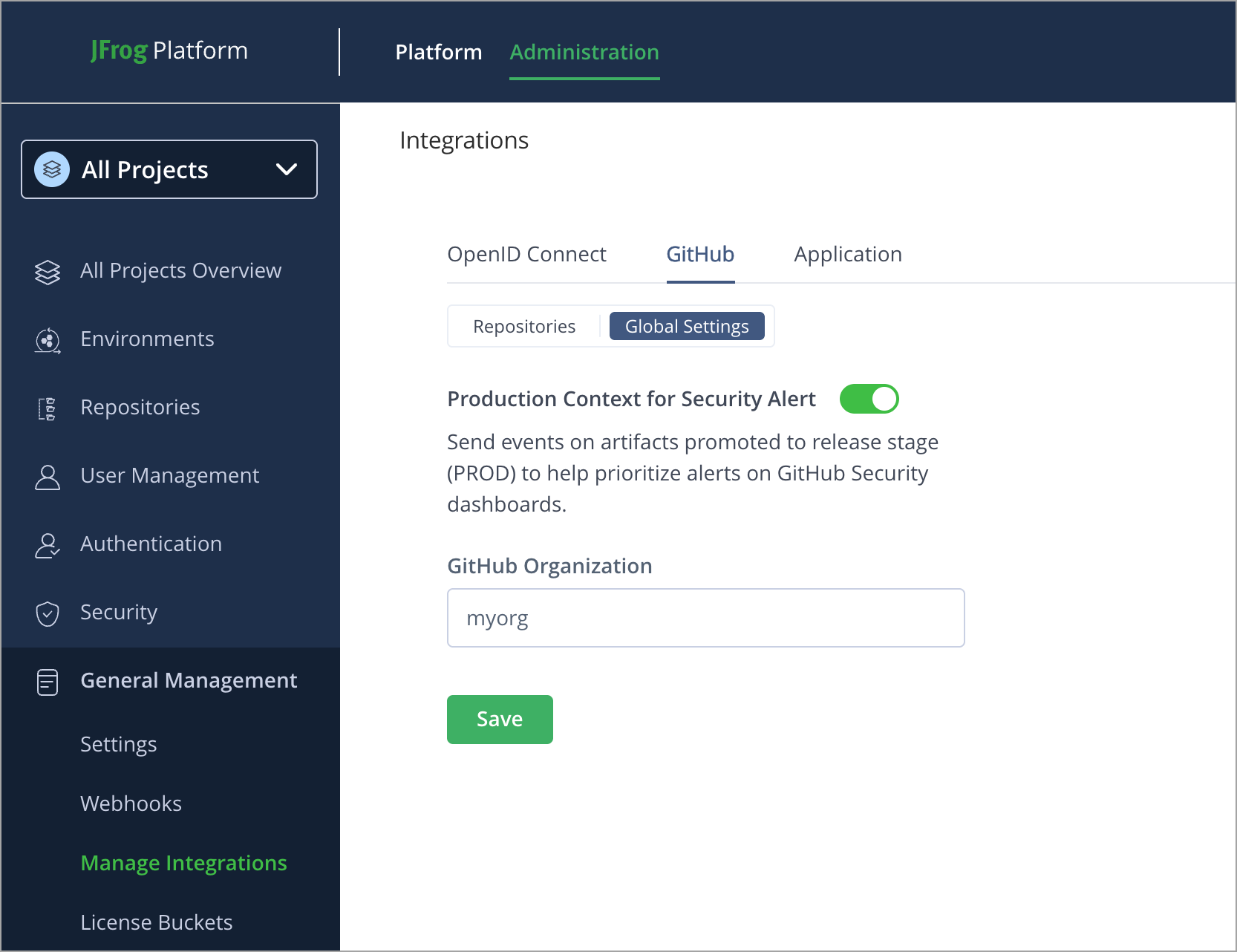
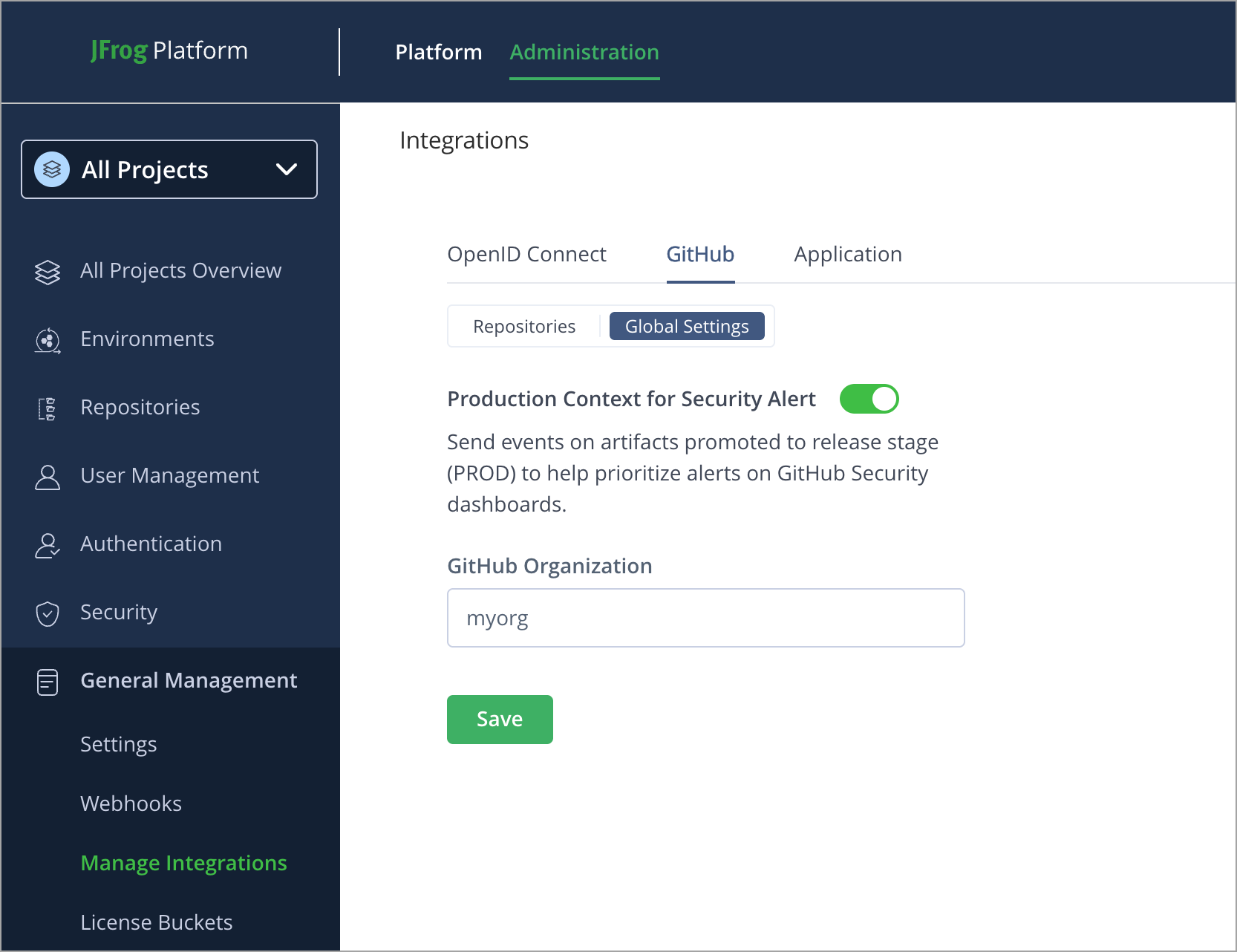
From the Administration module, click General Management | Manage Integrations | GitHub | Global Settings.
-
Click Activate.
-
In the Activate Dependabot modal, enter the name of your GitHub Organization, and then click Activate Dependabot.
Note
Once the integration is enabled, JFrog sends production promotion events to GitHub to prioritize security alerts.
Disable GitHub Dependabot
Disable Dependabot integration for the repositories you don’t want to be scanned.
-
From the Administration module, click General Management | Manage Integrations | GitHub | Global Settings.
-
Toggle the button to Disable the integration inline with the Production Context for Security Alert.
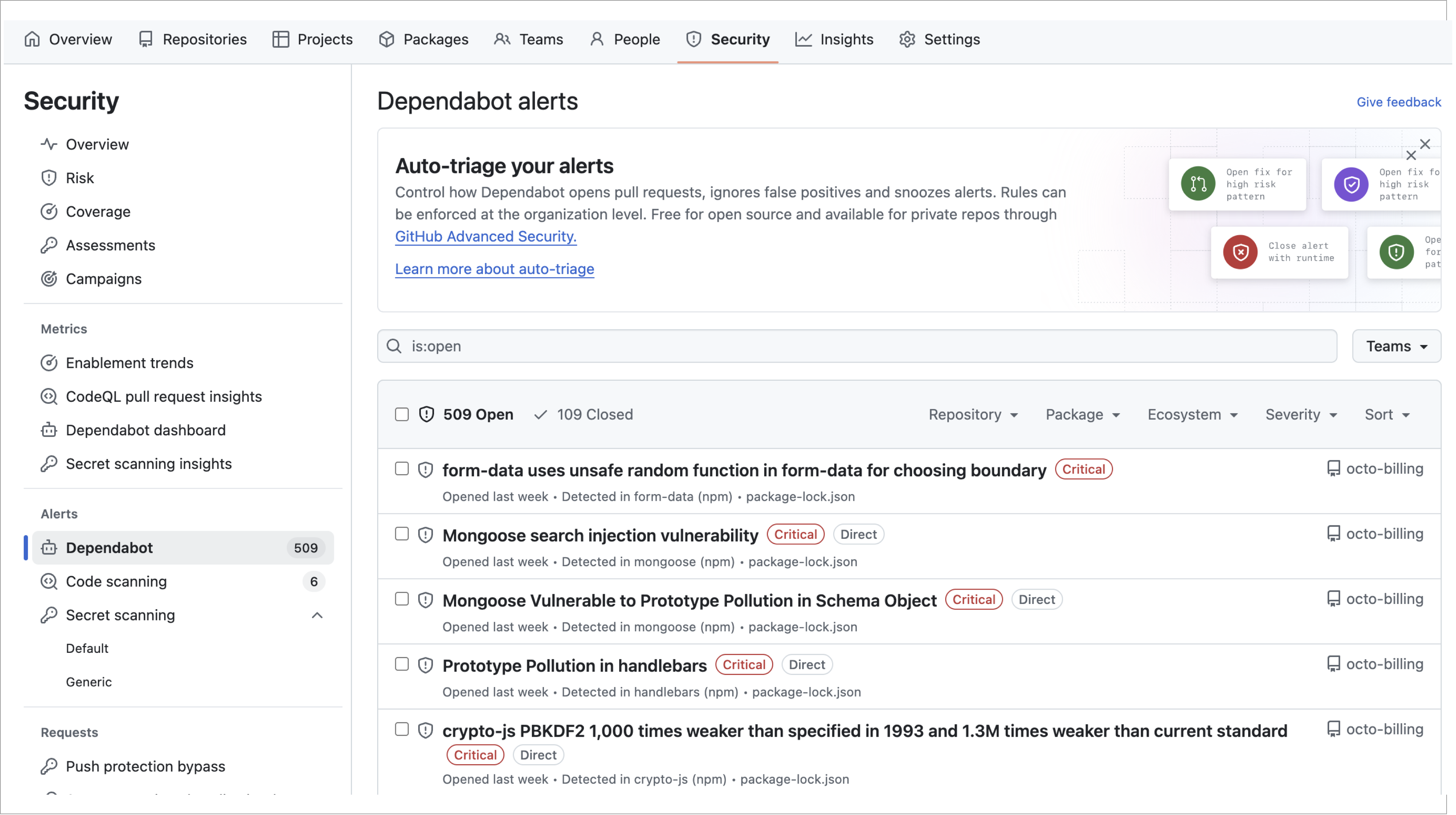
View JFrog Dependabot Vulnerability Alerts
This topic outlines the steps to view vulnerability alerts.
-
On GitHub, navigate to the main page of the repository.
-
Under the repository name, click Security. If you cannot see the Security tab, select the dropdown menu, and then click Security.
-
In the Vulnerability alerts sidebar of the security overview, click Dependabot. If this option is missing, it means you don't have access to security alerts and need to be given access. For more information, see Managing security and analysis settings for your repository.
-
In the Depedabot Alerts search field, filter by is:open package_registry:jfrog-artifactory.
You can also add additional filters by applying is:open package_registry:jfrog-artifactory severity:critical,high
To learn more, refer to Viewing Dependabot alerts.
JFrog and GitHub Integration Artifactory Administrator Workflow
This section describes JFrog Artifactory Administrator activities.
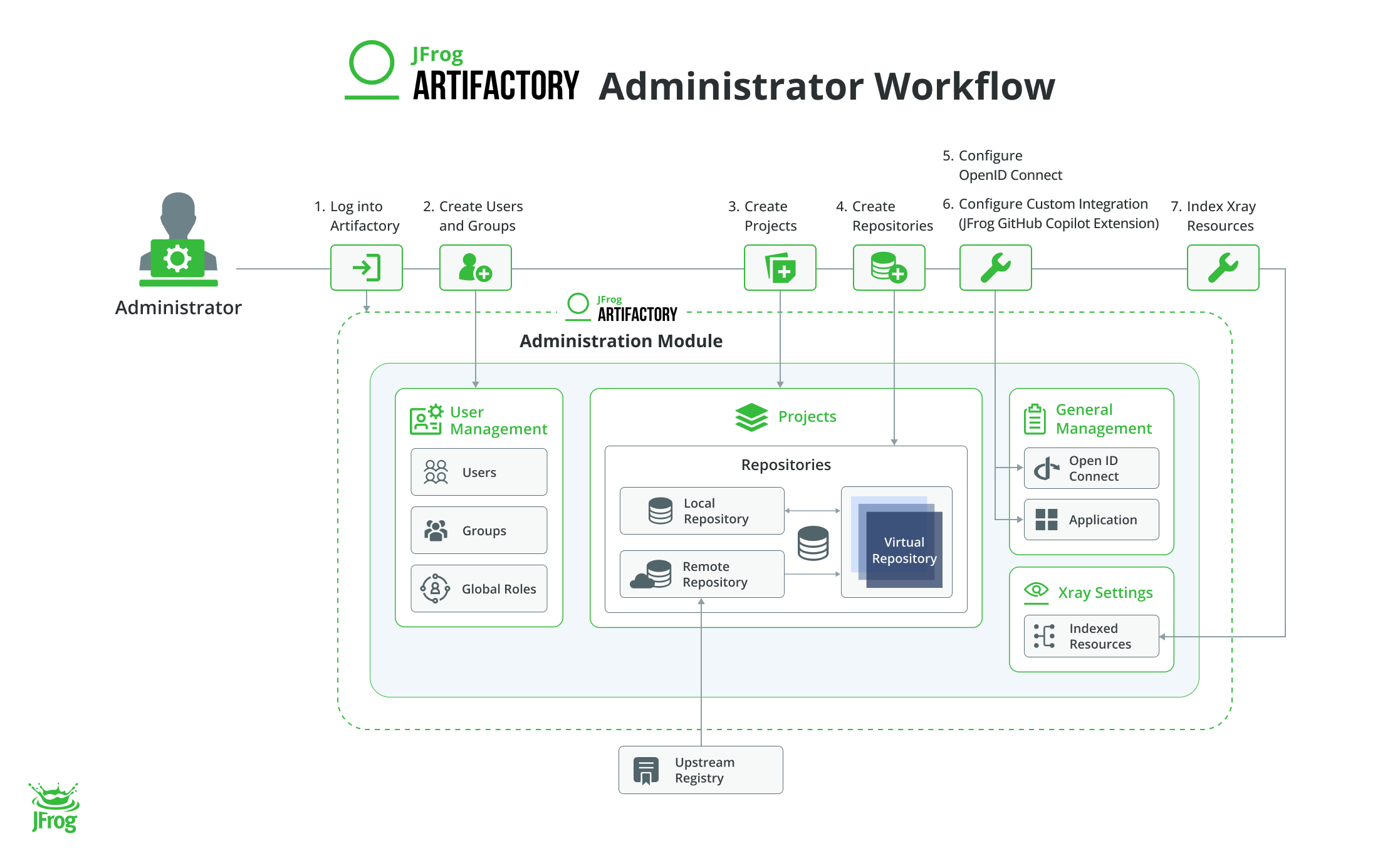
The following table describes JFrog Artifactory Administrator workflow activities:
Task | Description | For more information, see... | |
|---|---|---|---|
1 | Log into Artifactory | Log into Artifactory with your credentials | N/A |
2 | Create Users and Groups | Describes steps to add users and groups. Note: Creating users is mandatory. Group creation is optional. | |
3 | Create Projects (Optional) | Describes steps to add projects Note: This step is optional. We recommend using projects as a best practice. | |
4 | Create Repositories | Create related repositories | |
5 | Configure OpenID Connect (Optional) | Describes steps to configure OpenID Connect. Alternatively, you can use traditional credentials (username and password). Note: This step is optional. We recommend using OIDC as a best practice. | |
6 | Index repositories for Xray scans. | Describes steps to index resources for Xray scans | Index Xray Resources |
Configure OIDC in JFrog Platform
JFrog and GitHub integration using OpenID Connect (OIDC) establishes trust between GitHub Actions and the JFrog Platform. This setup automates token management and enhances security through OIDC for verifying identities. The OIDC provides a short-lived token for use in GitHub Actions, which can also be utilized with JFrog CLI.
Using OIDC in your workflows, allow GitHub Actions CI pipelines to download and publish artifacts without generating tokens and limit access to specific repos in Artifactory.
-
Seamless Access
Provides automatic, secure access to JFrog resources without manual token creation.
-
Enhanced Security
Provides short-lived tokens based on identity, applying tokens based on assigned privileges.
-
User Traceability
Identifies users performing actions on the JFrog Platform.
-
Passwordless Experience
Eliminates the need to store secrets.
GitHub Actions automatically builds and deploys artifacts to JFrog Artifactory. OIDC integration ensures secure and efficient authentication, maintaining compliance and traceability.
-
Reduce Configuration Errors
Use general OIDC parameters for GitHub configuration and identity mapping.
-
Configuration at Scale
-
Dynamic User Mapping
Automatically maps GitHub user identifiers instead of individually mapping each user.
-
Wildcard Support
Defines patterns for identity mapping, such as matching all repositories within an organization (for example,
"sub": "repo:name-org/*").
-
OIDC Projects Support
OIDC integration establishes a trust relationship between JFrog and GitHub Actions, specifically for JFrog projects.
Project-Specific Authorization: Enables Project Admins to create identity mappings with project-specific authorizations, linking GitHub repositories to JFrog Projects.
Advantages:
- Scalability: Delegates project admin tasks, reducing dependency on platform admins
- Team Isolation: Enhances data protection by isolating access
- Improved Performance: Minimizes conflicts
- Enhanced Security: Limits access to the scope of the project only
Project Admins can create identity mappings with project-level authorizations to connect GitHub repositories with JFrog Projects.
To learn more, refer to Integration with GitHub and Configuring OpenID Connect in JFrog.
JFrog and GitHub Integration GitHub Maintainer Workflow
This section illustrates GitHub and JFrog Integration Maintainer workflow diagram and the sequence of steps to be followed.
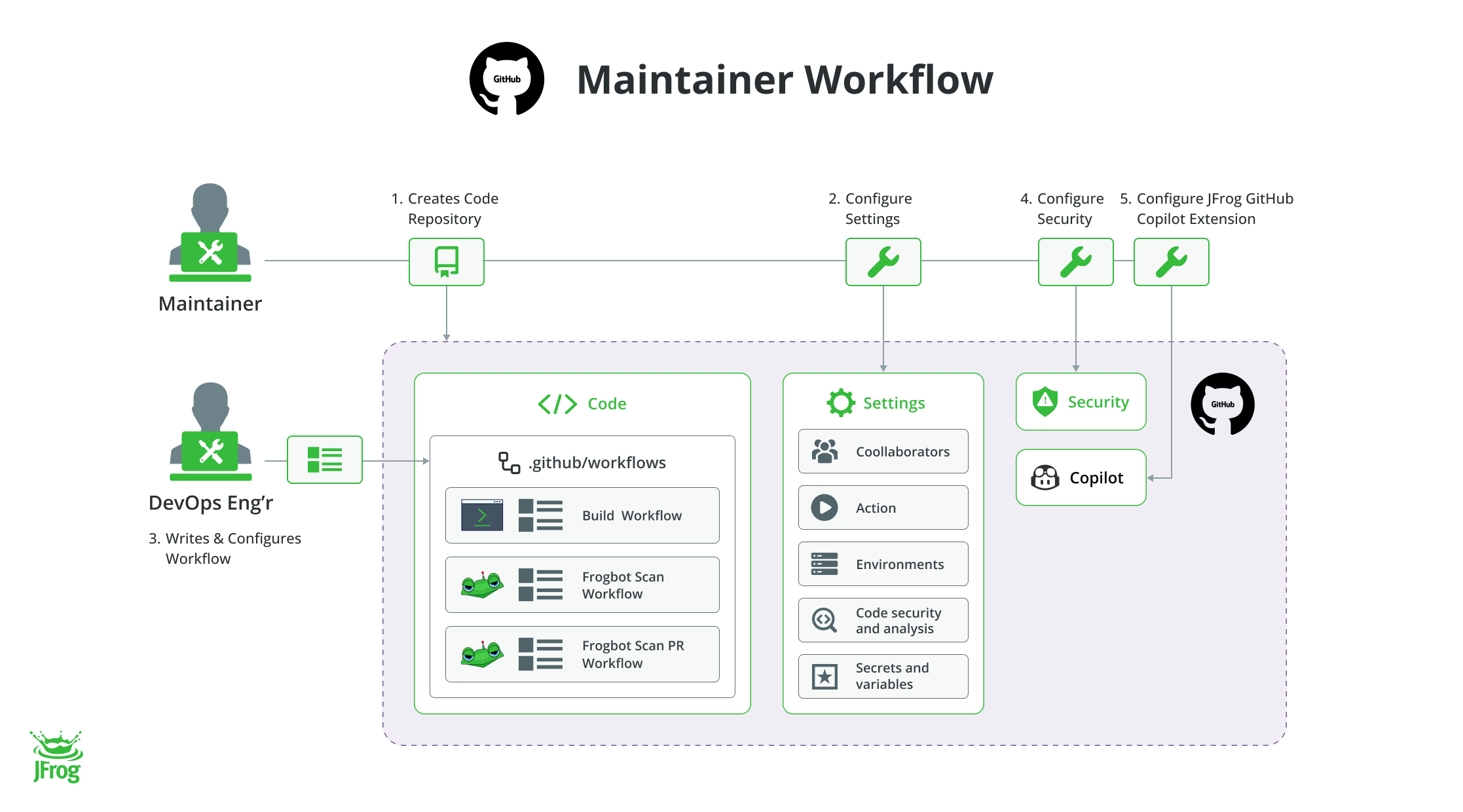
The following table describes GitHub maintainer workflow activities:
Task | Description | For more information, see... | |
|---|---|---|---|
1 | Create Code Repository | Creates code repository | Create a repository |
2 | Configure Settings | Configures settings in the repository | Managing GitHub Actions settings for a repository |
3 | Write Workflows | Writes workflows | Writing Workflows |
3.1 | Configure Workflows | Configures workflows | |
4 | Configure Security | Configures security | GitHub Advanced Security |
5 | Configure JFrog GitHub Copilot Extension | Configures JFrog GitHub Copilot Extension |
Configure GitHub Variables
Variables store and reuse non-sensitive configuration data, such as usernames, or server names. They are interpolated on the runner machine during your workflow. Commands in actions or workflow steps can create, read, and modify these variables.
Configure GitHub variables in your repository settings to point to JFrog.
Follow these steps to configure variables:
-
From your GitHub Repository Settings, click Secrets and variables.
-
Under Actions, click Variables, and then click New repository variable.
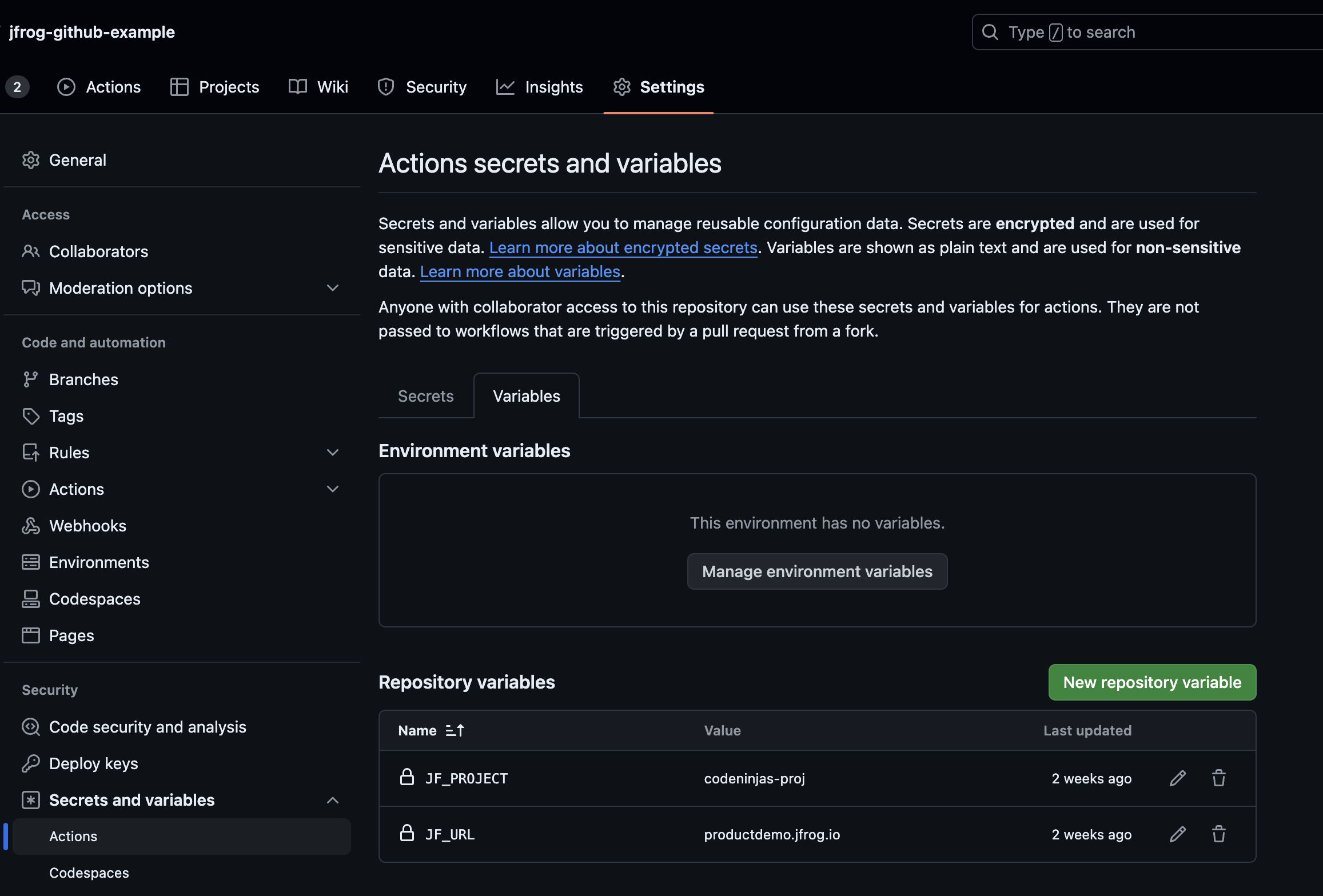
-
Add the following variables:
- JFrog Project Variable
- JFrog URL variable
To add a variable, add Name and Value, and then click Add variable.
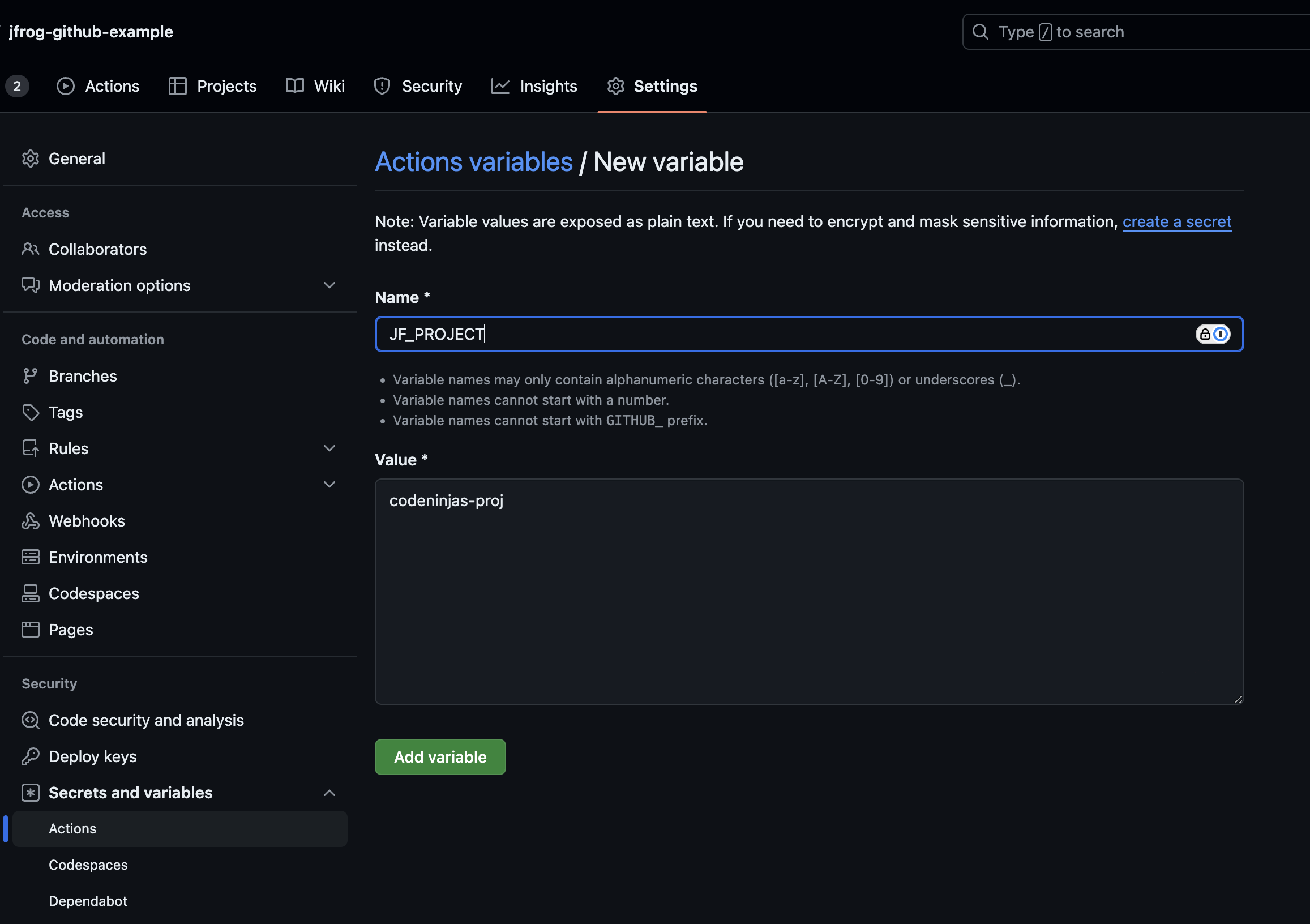
To learn more, refer to GitHub Actions Variables documentation.
Configure OIDC and GitHub Variables in GitHub Workflow
This section describes how to use variables and OIDC in the GitHub Actions workflow.
Example Usage
steps:
- name: Setup JFrog CLI
uses: jfrog/setup-jfrog-cli@v4
id: setup-cli
env:
JF_URL: https://${{ vars.JF_URL }}/
JF_PROJECT: ${{ vars.JF_PROJECT }}
with:
oidc-provider-name: <oidc_provider_name> #replace with the nameRelated Information
Configure Build Job
This section describes how to configure Build Job in GitHub workflow.
Build Info is collected using JFrog CLI for the following packages:
-
Supported through generic upload (
jf rt upload)- Generic
- NuGet
- Dotnet
- Pip
- Yarn
-
Supported natively (through integration with the native package manager or by wrapping the command in a jf command)
- Docker
- Generic
- Go
- Maven
- NPM
Example Usage
steps:
- name: Setup JFrog CLI
uses: jfrog/setup-jfrog-cli@v4
id: setup-cli
env:
JF_URL: https://${{ vars.JF_URL }}/
JF_PROJECT: ${{ vars.JF_PROJECT }}
with:
oidc-provider-name: <oidc_provider_name> #replace with the name
- name: Build and publish
run: |
jf pip install -r requirements.txt --module=jfrog-python-example
python setup.py sdist bdist_wheel
cd dist && echo "hashes=$(sha256sum * | base64 -w0)" >> $GITHUB_OUTPUT
jf rt u dist/ codeninjas-proj-python-virtual/example-projects/ --module=jfrog-python-exampleRelated Information
JFrog Evidence Management with GitHub Actions
This topic explains how to integrate GitHub Actions build attestations with JFrog's Evidence service to create a secure, verifiable audit trail for your software artifacts.
The idea is to create a secure and traceable link from your source code to the final build artifact.
- Generate Attestation in GitHub Actions: You use the
actions/attest-build-provenanceaction in your workflow to create a cryptographically signed attestation. This attestation follows the SLSA and in-toto frameworks, providing verifiable proof of where and how your artifact was built. - Push to JFrog Artifactory: Your workflow pushes the built artifact (for example, a Docker image, a binary) to JFrog Artifactory.
- Ingest into JFrog Evidence: The integration automatically ingests the build attestation from GitHub into JFrog Evidence. It intelligently links this attestation to the specific artifact stored in Artifactory.
By integrating them, you ensure that every artifact in Artifactory has a verifiable history, which is crucial for security, compliance, and auditing. Attestations of build provenance that you generate with the GitHub Action can be automatically sent to and stored within JFrog Evidence.
Sample Workflow
- Code Push: A developer pushes code to your GitHub repository.
- Build Trigger: A GitHub Actions workflow starts.
- Build and Push Artifact: The workflow builds your artifact (for example, a Docker image) and pushes it to a repository in JFrog Artifactory.
- Generate and Store Evidence: The
attest-build-provenanceaction generates the signed attestation. Because of the native integration (which occurs in the postjfrog/setup-jfrog-clistep), this attestation is automatically sent to your JFrog Platform and stored as evidence linked directly to the newly pushed artifact.
Ensure your workflow has the correct permissions to write attestations and use OIDC.
# This workflow demonstrates building a Docker image, pushing it to JFrog Artifactory,
# and attaching an SLSA build provenance attestation, which is stored in JFrog Evidence.
name: Build, Push, and Attest to JFrog
on:
push:
branches:
- main
workflow_dispatch:
# Use GitHub variables (vars) and secrets (secrets) for configuration
env:
JF_REGISTRY: ${{ vars.JF_REGISTRY }}
JF_DOCKER_REPO: ${{ vars.JF_DOCKER_REPO }}
IMAGE_NAME: ${{ vars.IMAGE_NAME }}
jobs:
build-and-attest:
runs-on: ubuntu-latest
permissions:
contents: read
packages: write
id-token: write # Required for OIDC token access
attestations: write # Required for attestation
steps:
- name: Checkout Code
uses: actions/checkout@v4
- name: Set up Docker Buildx
uses: docker/setup-buildx-action@v3
- name: Install and Configure JFrog CLI
id: setup-jfrog-cli
uses: jfrog/[email protected]
env:
JF_URL: ${{ secrets.JF_URL }}
with:
# Replace with the name of your configured OIDC provider in JFrog
oidc-provider-name: 'your-github-oidc-provider-name'
- name: Log in to JFrog Docker Registry
uses: docker/login-action@v3
with:
registry: ${{ env.JF_REGISTRY }}
username: ${{ steps.setup-jfrog-cli.outputs.oidc-user }}
password: ${{ steps.setup-jfrog-cli.outputs.oidc-token }}
- name: Build and Push Docker Image
id: build-and-push
uses: docker/build-push-action@v6
with:
context: .
push: true
tags: ${{ env.JF_REGISTRY }}/${{ env.JF_DOCKER_REPO }}/${{ env.IMAGE_NAME }}:${{ github.run_number }}
- name: Attest Docker Image and Send to JFrog Evidence
uses: actions/attest-build-provenance@v3
with:
# The 'oci://' prefix is required by JFrog to correctly parse the artifact type
subject-name: oci://${{ env.JF_REGISTRY }}/${{ env.JF_DOCKER_REPO }}/${{ env.IMAGE_NAME }}
# This links the attestation directly to the image digest from the build step
subject-digest: ${{ steps.build-and-push.outputs.digest }}Related Information
Security Scans
JFrog Frogbot scans your repositories for vulnerabilities, exposed secrets, and malware in dependencies. When it detects issues, it alerts you and can automatically create pull requests with suggested fixes to streamline remediation. This helps prevent unauthorized or risky code changes from being merged.
Additionally, Frogbot provides detailed reports and dashboards to assist with compliance and offer insights into your projects' security posture.
-
Results are displayed on the GitHub Advanced Security Dashboard and in JFrog Xray's Scan List section (SaaS only) for branch commits. To learn more, refer to View Xray Scan Results.
-
Pull request scans provide findings as comments within the pull request. Detected issues cover SCA (Software Composition Analysis) concerns like vulnerable dependencies, malicious packages, and licensing violations. To learn more, refer to Software Composition Analysis.
-
JFrog Advanced Security issues include the following checks:
- SAST (Static Application Security Testing)
- Contextual Analysis
- Secrets detection
- IaC (Infrastructure as Code)
To learn more, refer to JFrog Advanced Security
Configure Frogbot in GitHub Actions
Frogbot scans your repository periodically or on-demand for exposed secrets, malware, and vulnerabilities, alerting you through GitHub security advisories. Upon detecting vulnerabilities, Frogbot alerts you and can initiate pull requests with suggested fixes, simplifying remediation and preventing unauthorized or risky code merges.
Additionally, Frogbot offers detailed reports and dashboards to aid compliance and provide insights into your project's security posture.
Refer to Setup Frogbot Using GitHub Actions instructions on configuring Frogbot in GitHub.
- uses: jfrog/frogbot@v2
with:
oidc-provider-name: jfrog-github-oidc
env:
JF_URL: https://${{ vars.JF_URL }}/
JF_GIT_TOKEN: ${{ secrets.GITHUB_TOKEN }}
JF_PROJECT: ${{ vars.JF_PROJECT }}Refer to Frogbot Scan workflow for an example workflow.
GitHub PR Scans and Advanced Security
Adding Frogbot to your GitHub repository enables pull request checks based on Frogbot code scanning, preventing unauthorized or risky code changes from being merged.
Example Usage
Here is an example snippet of GitHub Action workflow for PR scan using Frogbot.
name: "Frogbot Scan Pull Request"
on:
pull_request_target:
types: [ opened, synchronize ]
permissions:
pull-requests: write
contents: read
id-token: write
jobs:
scan-pull-request:
runs-on: ubuntu-latest
# A pull request needs to be approved, before Frogbot scans it. Any GitHub user who is associated with the
# "frogbot" GitHub environment can approve the pull request to be scanned.
# Read more here (Install Frogbot Using GitHub Actions): https://github.com/jfrog/frogbot/blob/master/docs/install-github.md
environment: frogbot
steps:
- uses: actions/checkout@v2
with:
ref: ${{ github.event.pull_request.head.sha }}
# IMPORTANT:
# 1. See the following link for information about the tools that need to be installed for Frogbot to work - https://github.com/jfrog/frogbot/tree/master/docs/templates/github-actions/scan-and-fix
# 2. Some projects require creating a frogbot-config.yml file. Read more about it here - https://github.com/jfrog/frogbot/blob/master/docs/frogbot-config.md
- uses: jfrog/frogbot@v2
with:
oidc-provider-name: jfrog-github-oidc
env:
JFROG_CLI_LOG_LEVEL: DEBUG
# JFrog platform URL
JF_URL: https://${{ vars.JF_URL }}/
JF_PROJECT: ${{ vars.JF_PROJECT }}
# The GitHub token automatically generated for the job
JF_GIT_TOKEN: ${{ secrets.GITHUB_TOKEN }}To learn more, refer to the following:
Scan Builds
Using GitHub Actions pipeline, you can scan published builds for SCA issues, such as vulnerable dependencies, malicious packages, and license violations. Scan summaries are shown in the Job Summary, with detailed results in both the GitHub Action logs and the JFrog platform's Builds section.
To learn more, refer to Scan Published Builds and Understand Xray Scan Results.
Example Usage
steps:
- name: Scan Published Build with Xray
run: |
jfrog xr scan --build="my-build-name" --build-number="18"Scan Binaries
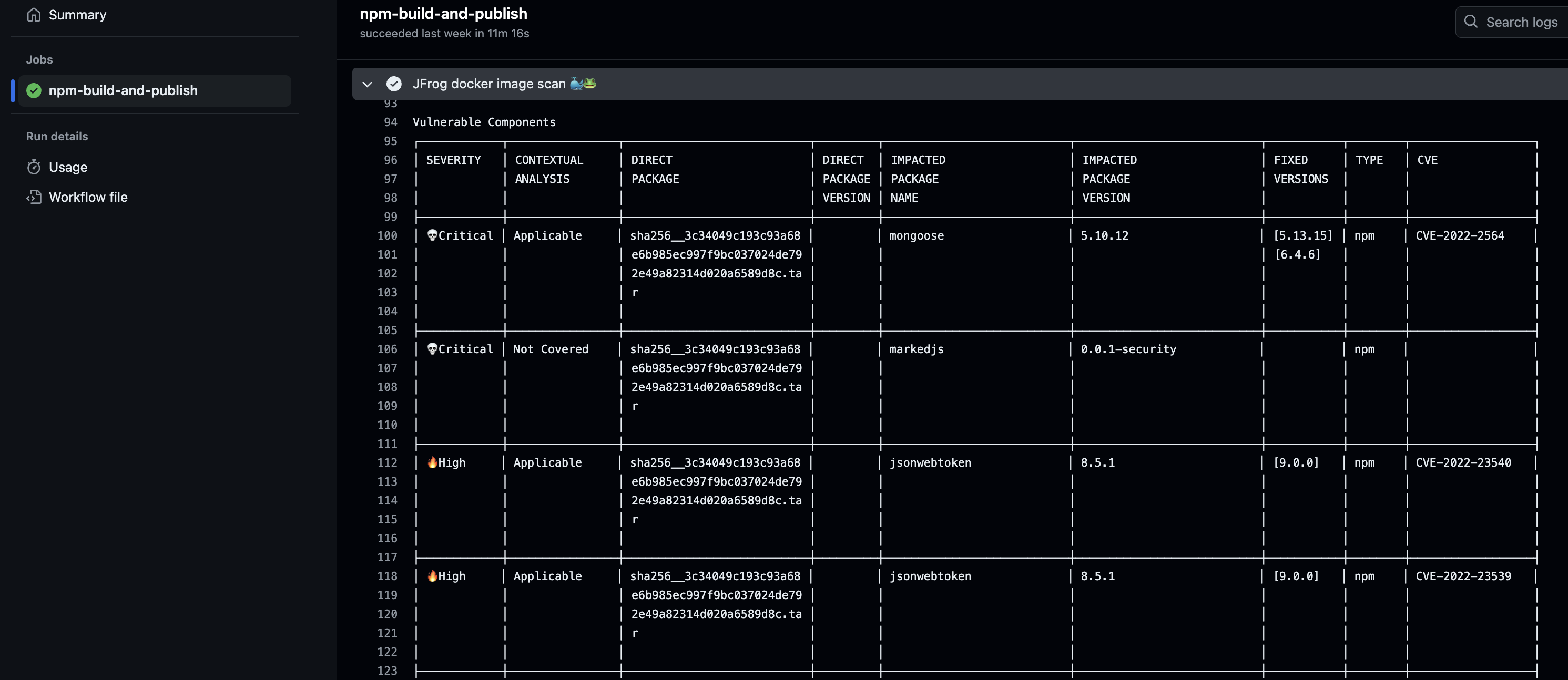
Using GitHub Actions pipelines, you can scan binaries for SCA issues, such as vulnerable dependencies, malicious packages, and license or operational risks, before uploading them to Artifactory. For Docker images, Contextual Analysis and Secrets Detection JFrog Advanced Security scanners are also activated. Scan summaries appear in the Job Summary, while detailed results are available in the GitHub Action logs and under the On Demand Scanning section in the JFrog platform.
Example Usage
- name: Docker Build 🐳🐸
run: |
jf docker build . -t ${{ vars.JF_URL }}/${{ vars.DOCKER_REPO }}/${{ env.IMAGE_NAME }}:${{github.run_number}}
- name: JFrog docker image scan 🐳🐸
run: |
jf docker scan ${{ vars.JF_URL }}/${{ vars.DOCKER_REPO }}/${{ env.IMAGE_NAME }}:${{github.run_number}}
- name: Docker Push 🐳🐸
run: |
jf docker push ${{ vars.JF_URL }}/${{ vars.DOCKER_REPO }}/${{ env.IMAGE_NAME }:${{github.run_number}}To learn more, refer to the Build Workflow.
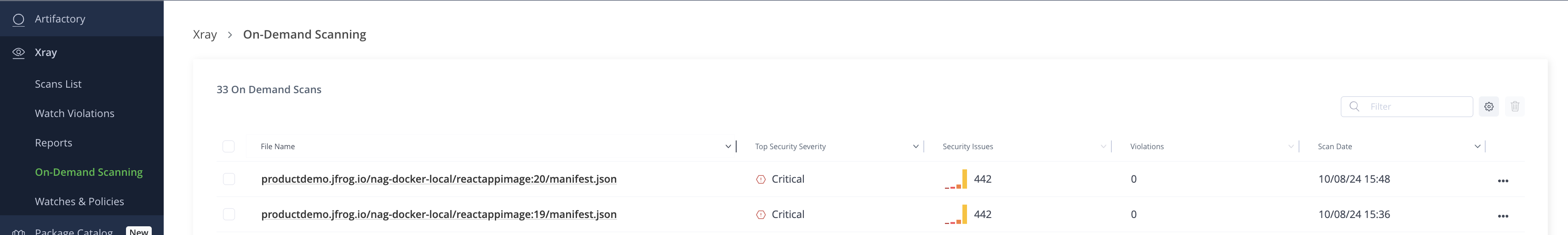
On-Demand Scanning
To view On-Demand Scanning results, follow these steps:
-
From the Application Module, click Xray, and then click On-Demand Scanning.
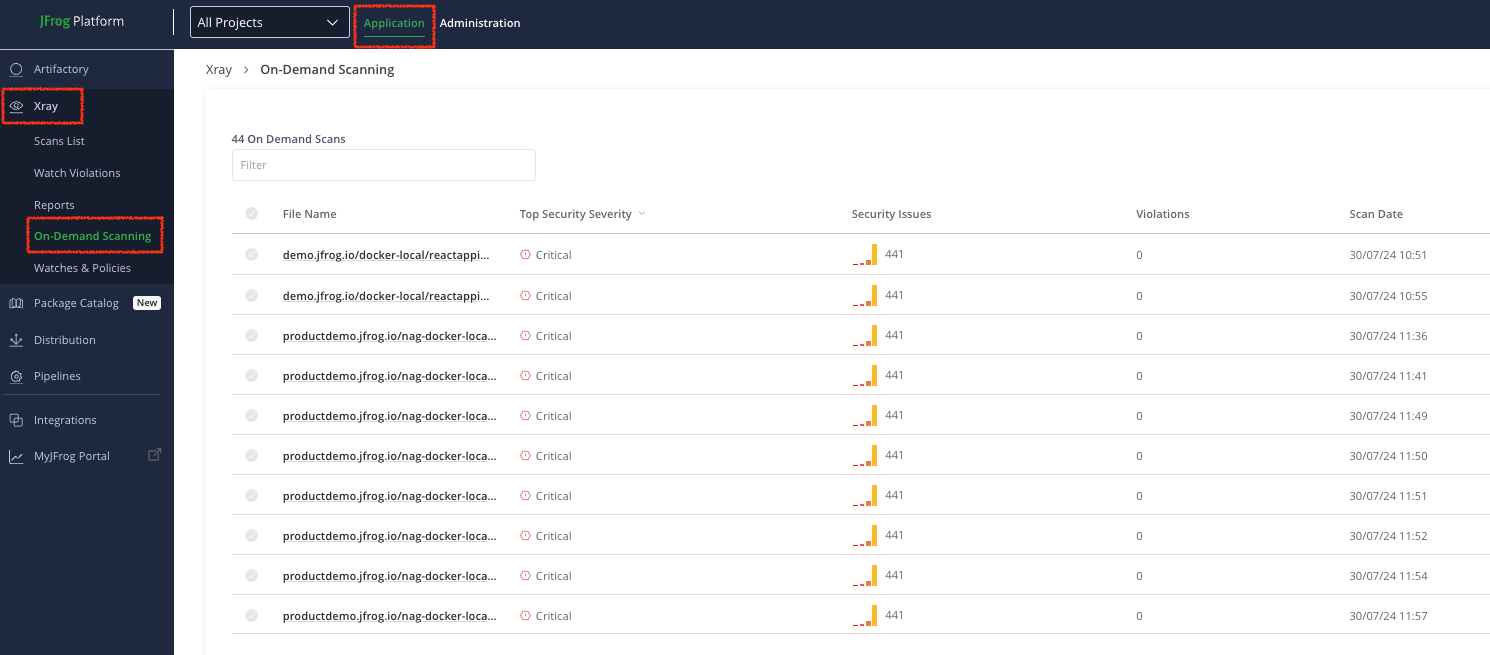
-
From the On-Demand Scanning list, click the file you want to view.
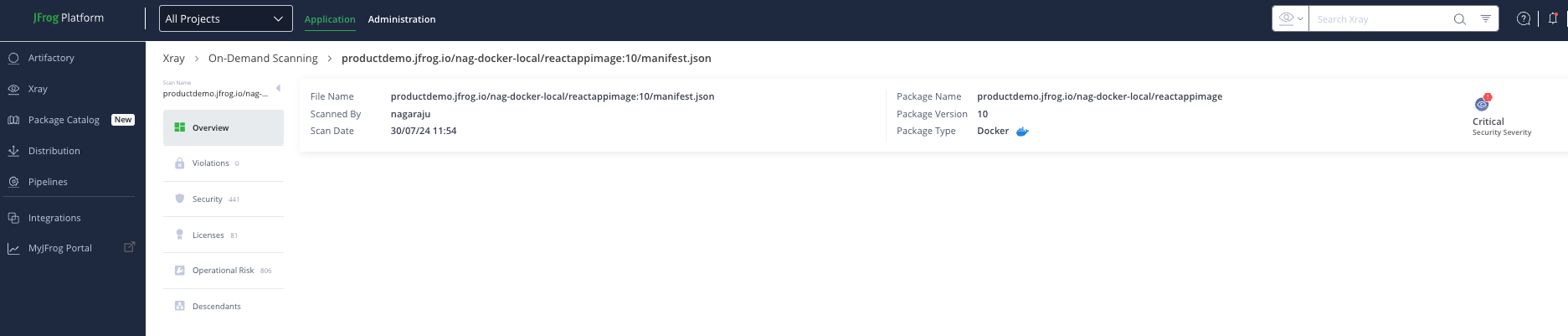
To learn more, refer to On Demand Scanning documentation.
Curation Audit
Frog Curation protects your software supply chain by blocking malicious or risky open-source packages before they enter. The Job Summary lists specific package policy violations that led to their blockage and receives recommendations for alternative, policy-compliant package versions.
Feature Limitation
To view insights in the GH Job Summary, you must:
-
Include a step with the command
jf curation audit.steps: - name: Run JFrog Curation Audit run: jf curation audit -
Use JFrog CLI commands (for example,
jf pip install,jf maven install) instead of package manager commands.steps: - name: Install Python dependencies run: pip install -r requirements.txt
To learn more, refer to Curation Overview and CLI for JFrog Curation.
JFrog and GitHub Integration Developer Workflow
This section illustrates GitHub and JFrog Integration Developer workflow diagram and the sequence of steps to be followed.
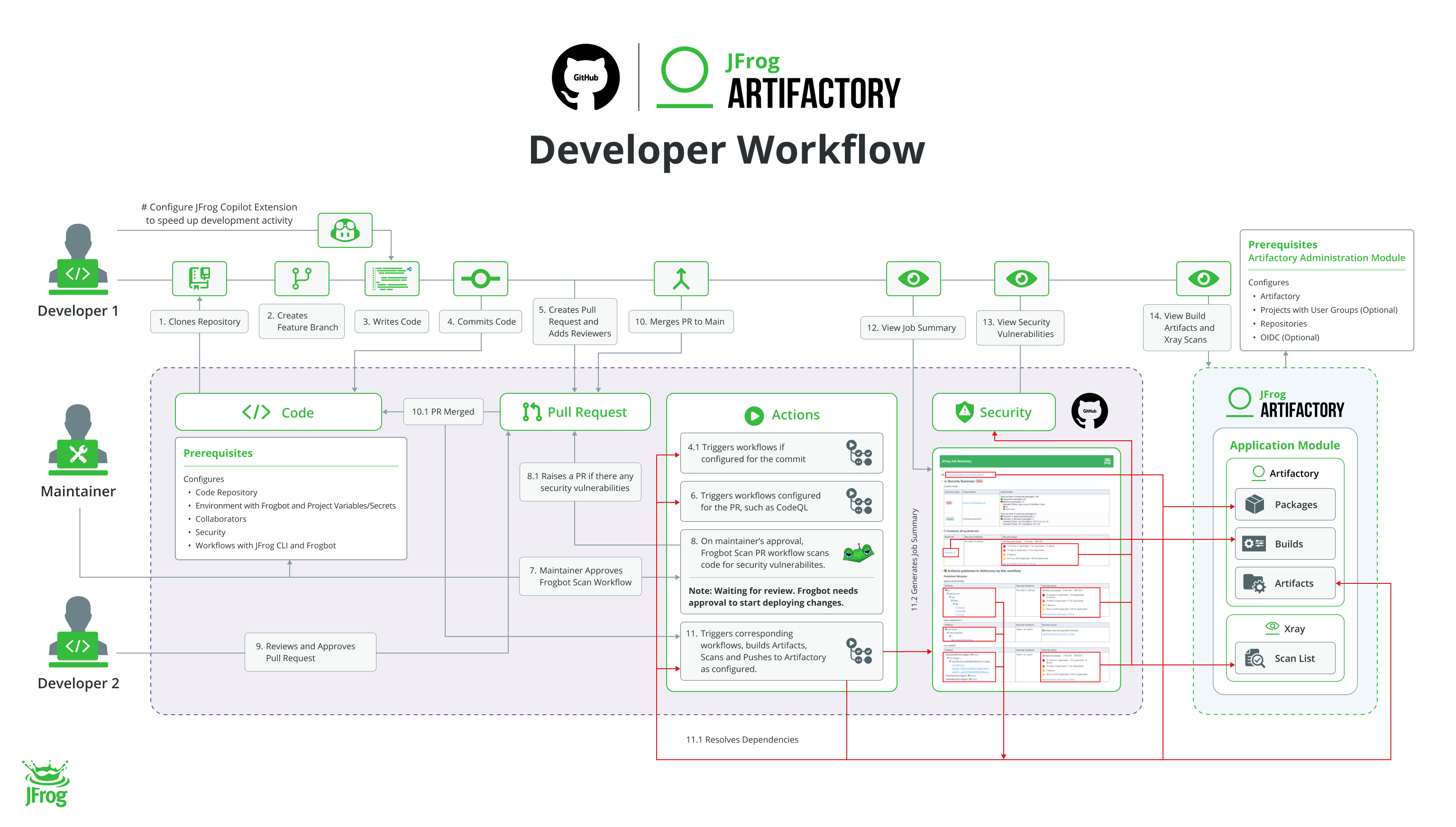
Prerequisites
The following are the prerequisites for the developer's workflow:
- JFrog and GitHub Integration Artifactory Administrator Workflow
- JFrog and GitHub Integration GitHub Maintainer Workflow
The following table describes GitHub and JFrog Integration Developer workflow steps:
Task | Description | For more information, see... | |
|---|---|---|---|
Configure JFrog GitHub Copilot Extension in IDE | Configures JFrog GitHub Copilot Extension in IDE | ||
1 | Clone Repository | Clones repository | Cloning a repository |
2 | Create Feature Branch | Creates feature branch | Creating a branch |
3 | Write Code | Writes code. Use Configure JFrog GitHub Copilot Extension in IDE to speed up development activity. | |
4 | Commit Feature Code | Commits feature code to their branch repository | Pushing commits to a remote repository |
4.1 | Trigger Workflows | Triggers workflows if configured for the commit | NA |
5 | Create Pull Request (PR) | Creates PR on GitHub and adds reviewers to review their code | Creating a pull request |
6 | Trigger Workflows | Triggers corresponding workflows. Frogbot scan PR workflow waits for the maintainer's approval | Triggering a workflow |
7 | Approve Frogbot Scan Workflow | Maintainer approves Frogbot Scan Workflow | Scan GitHub Pull Request |
8 | Trigger Frogbot Scan Workflow | On maintainer's approval, Frogbot scan PR workflow scans code for security vulnerabilities | NA |
8.1 | Security Vulnerabilities | If there are any security vulnerabilities, Frogbot opens a PR for resolving the vulnerabilities | Pull Request Scan Results |
9 | Review PR and Approve | Reviewer reviews the PR and approves it | Approving a pull request with required reviews |
10 | Merge PR | Developer merges PR with the main branch. | Merging a pull request |
11 | Trigger Workflows | Triggers workflows, builds artifacts, scans, pushes to Artifactory as per the configuration | Triggering a workflow |
11.1 | Resolve Dependencies | Resolves dependencies as required by the workflow | N/A |
11.2 | Generates Job Summary | Generates Job Summary | NA |
12 | View Job Summary | On successful merging, workflows are triggered and pushes build artifacts to Artifactory and Security results to Xray as configured. The workflow generates a job summary. | |
13 | View Security vulnerabilities | View scan results on GitHub Advanced Security Dashboard | |
14 | View Build Artifacts and Xray Scans in Artifactory | Refer Artifactory and Xray on JPD platform to learn about the produced artifacts and security results. |
View JFrog Job Summary
A job summary with build and security information is generated once the build run is complete. You can seamlessly navigate between JFrog and GitHub platforms. Additionally, you can view more details about your artifacts and security scans by clicking on the project package link, which takes you to the JFrog project packages view.
For packages uploaded using generic upload (jf rt upload) as well as Docker, NPM, Maven and Go the Job Summary contains:
-
A link to the corresponding Build page in Artifactory
-
A list of the published modules with their artifact tree.
Each artifact links to its corresponding artifact in Artifactory.
To view JFrog Job Summary on GitHub, follow these steps:
From the Actions tab, click the corresponding workflow, and then click Summary to view JFrog Job Summary.
You can navigate between the job summary and corresponding JFrog Artifactory areas as follows:
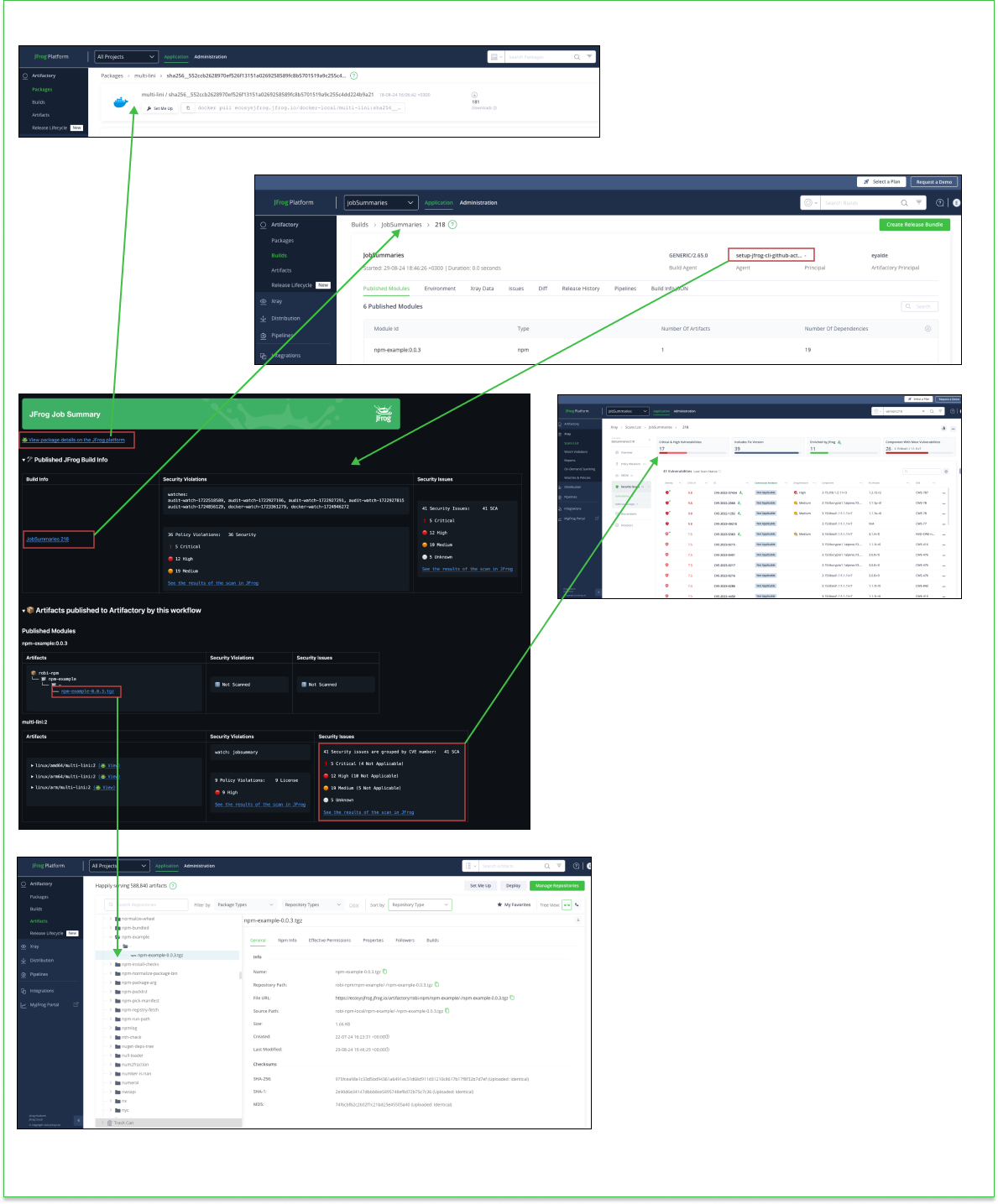
Project Packages
Click the Project Packages to navigate to packages page in the Artifactory.
Build Info Published to Artifactory
Click the build-info link to navigate to the build-info page in the Artifactory. Here, you can view access details such as Published Modules, Environment, Xray Data, and Build Info JSON information. To learn more, refer to View Build Number Information.
Files Uploaded to Artifactory
Each artifact will link to its corresponding Artifactory artifact.
Security Status
Contains summary of security issues detected by the following in the workflow:
- jf build-info scan
- jf scan
- jf docker scan
You can also view those details in:
-
GitHub Job Console
-
Xray - On-Demand Scanning
-
Xray - Scan List - Builds
Curation
Contains a summary of security issues detected during the workflow.
Build Page Linkage
Click Agent link in the build-info to navigate to GitHub.
To learn more, refer to JFrog Job Summary.
Note
Other supported packages, OCI, Gradle, and Terraform, have a link to the Artifactory build, but not to the artifacts.
Docker packages have a temporary limitation on integration.
To generate the relevant build info and Job Summary, refer to the Manifest List.
Build and push multi platforms image:
> docker login DOCKER_REG_URL
> docker buildx install
> docker buildx create --use --name mybuilder --driver docker-container
> docker buildx build --platform=linux/amd64,linux/arm64,linux/arm/v7 --tag=DOCKER_REG_URL/TARGET_REPO/multiarch-image:1 -f=Dockerfile.Fatmanifest --metadata-file=build-metadata --push .
Configure Artifactory:
> jf c add --url=<JFROG_PLATFORM_URL> [credentials flags]
Collect image build info:
> jf rt build-docker-create TARGET_REPO --server-id=MY_SERVER_ID --image-file build-metadata --build-name myBuild --build-number 1
Publish build info:
> jf rt build-publish --server-id=MY_SERVER_ID myBuild 1
Remove buildx alias
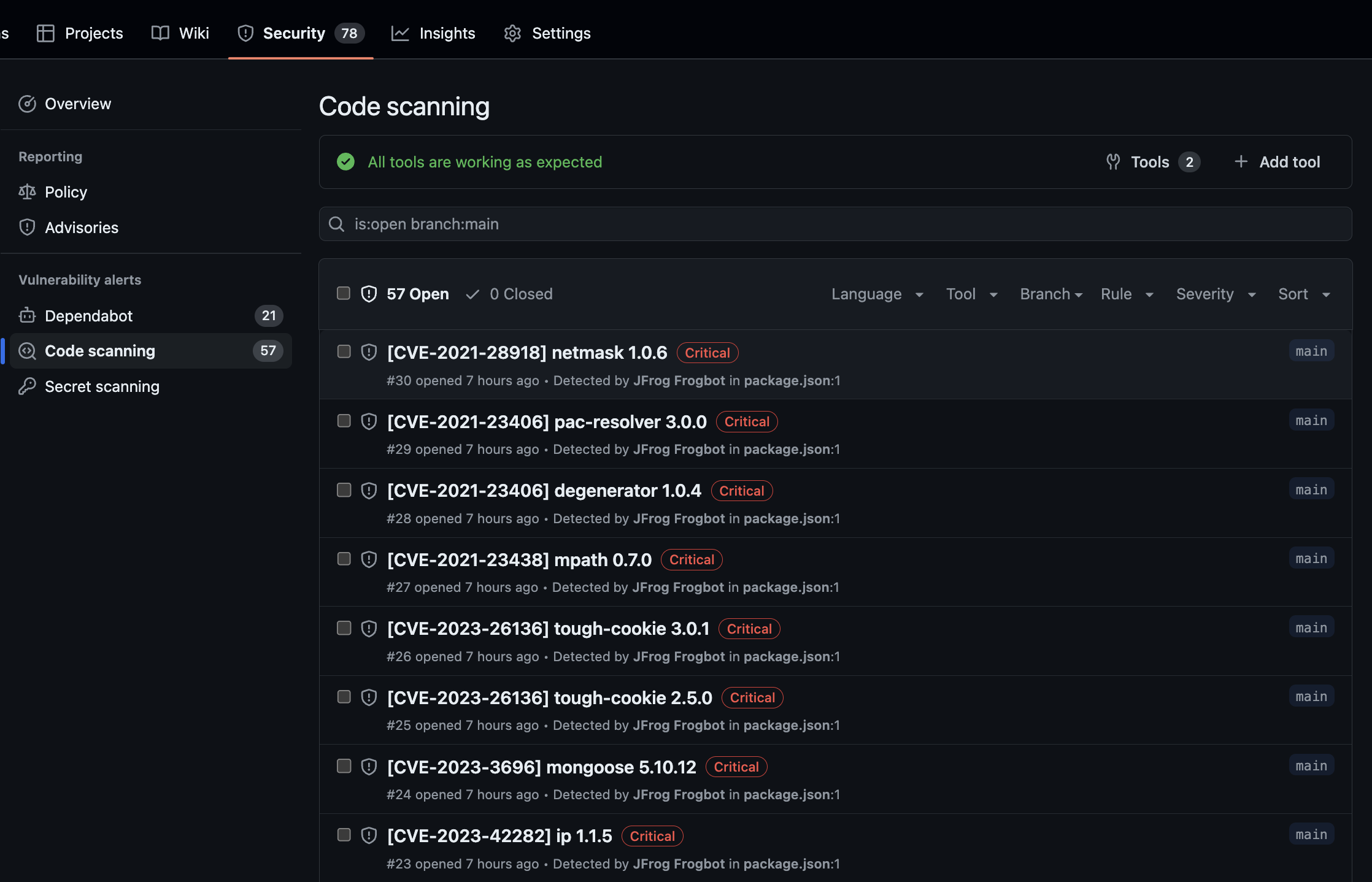
> docker buildx uninstallView GitHub Advanced Security Results
A unified security dashboard for GitHub Advanced Security and other scanning results (JFrog Advanced Security). You can see a comprehensive security view of the codebase.
Analyzes source code for security issues, including Software Composition Analysis (SCA), contextual analysis, secrets detection, Static Application Security Testing (SAST), and Infrastructure as Code (IaC).
Scans Docker images for secrets and vulnerabilities, with results integrated into the GitHub Advanced Security dashboard.
You can view detected secrets in Docker image scanning results on the GitHub Advanced Security Dashboard under the Security > Code Scanning section.
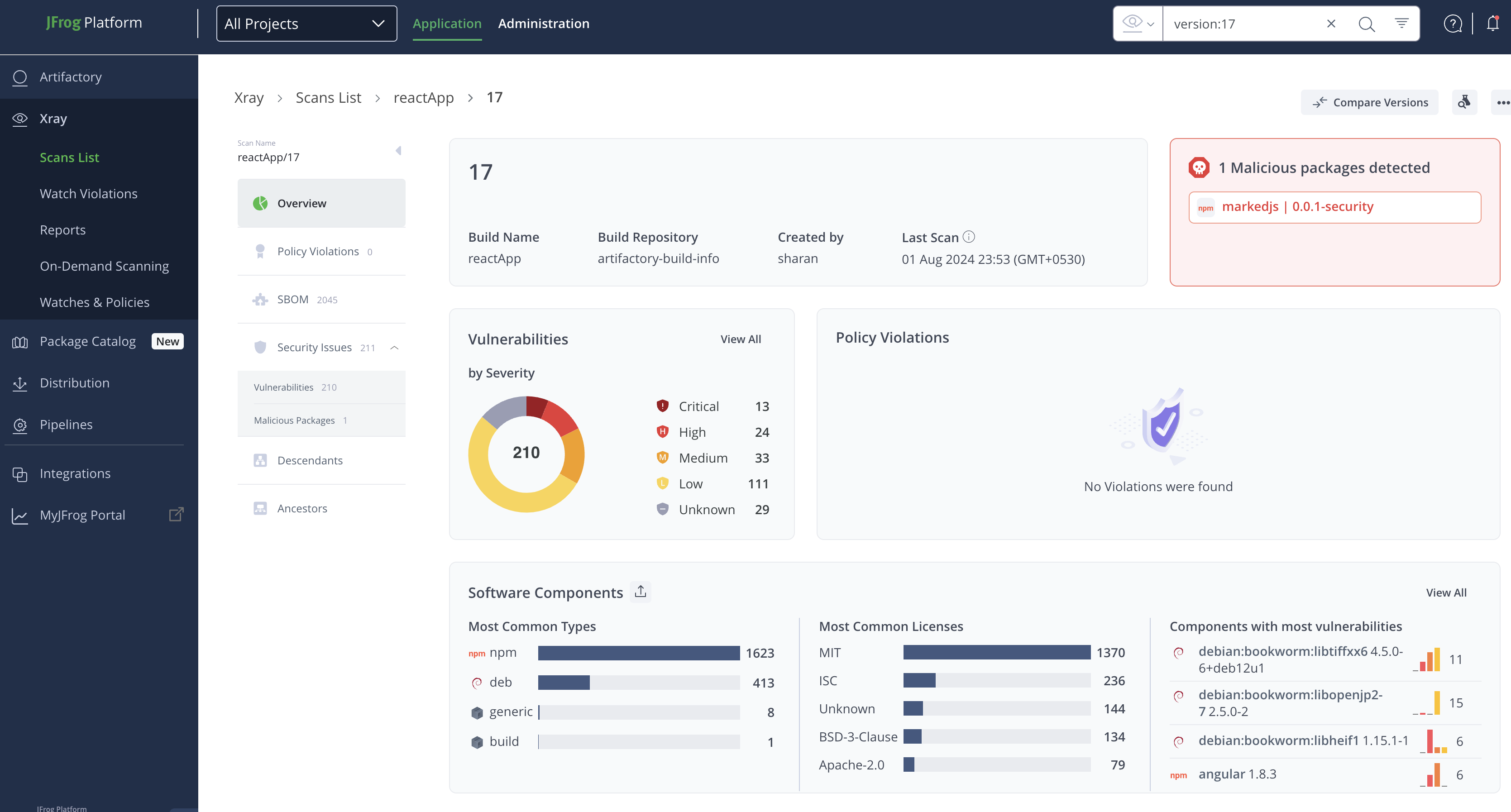
View Xray Scan Results
Xray scan results provide a single screen and enable you to view details of the following:
- Git Repositories
- Repositories
- Builds
- Release Bundles
- Packages
For each of the above items, you can drill down further to view the report overview, policy violations, components, and security issues.
To view Scan Results, from the Application Module, click Xray, and then click Scan List.
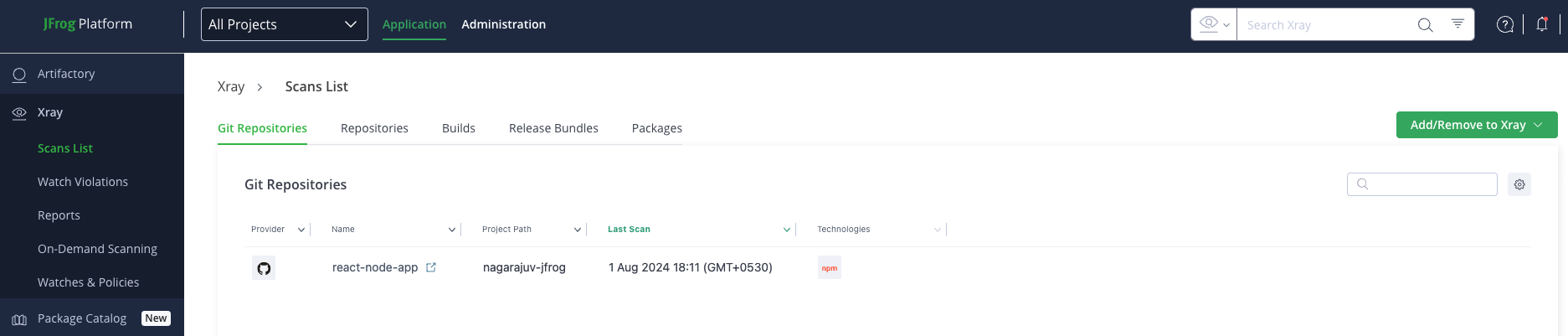
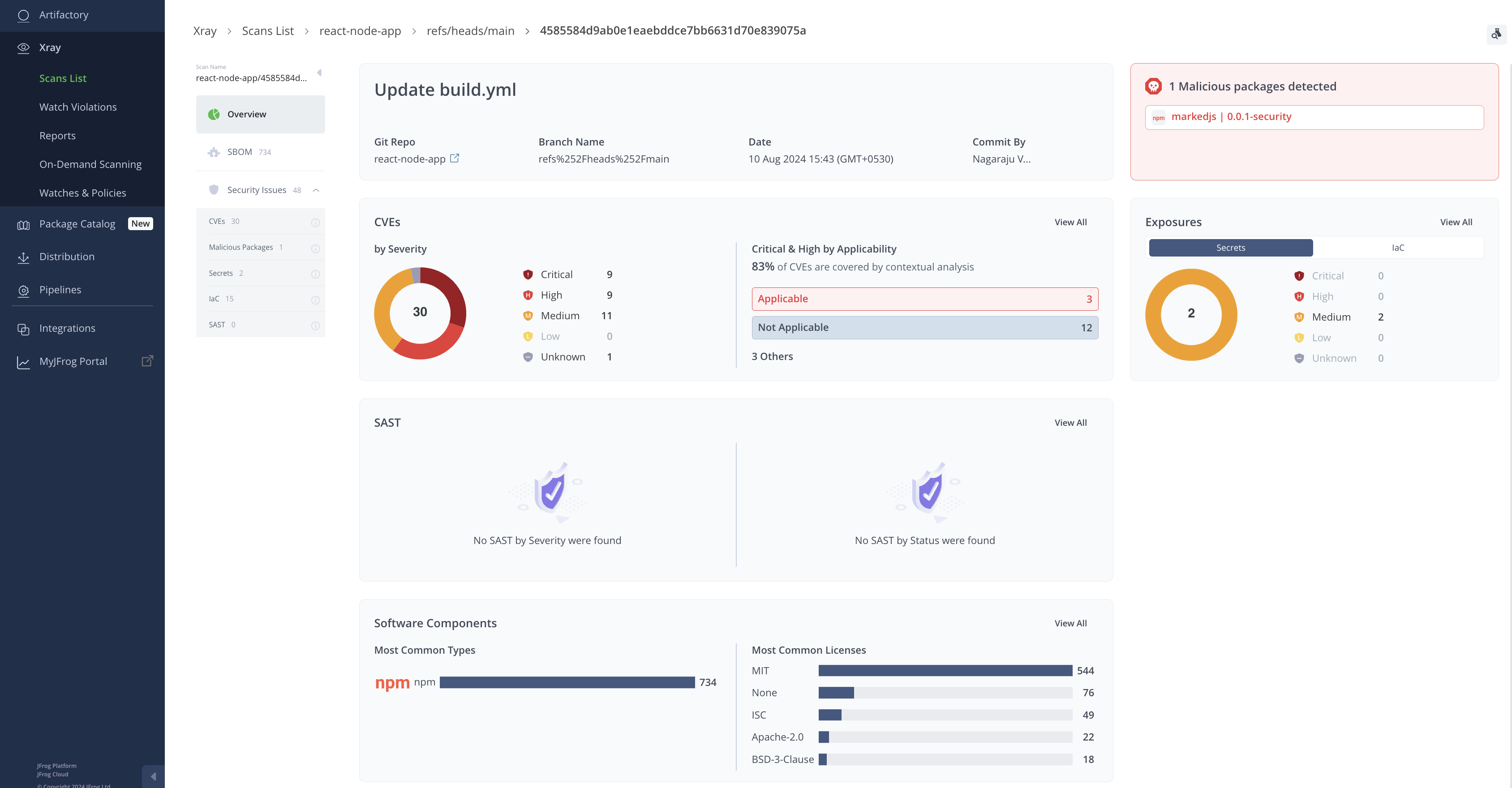
To learn more, refer to Understanding and Analyzing Xray Scan Results.
Updated 3 months ago

