Security Keys Management
Subscription Information
This feature is supported with the Enterprise+ license.
The Keys Management function in the JFrog Platform enables you to create and control the keys used to encrypt or digitally sign your artifacts - in one central location. This makes it easier for you to manage signing keys throughout your organization.
Using the Keys Managed function, you can configure the following Artifactory security settings:
- Signing Keys: Use this tab to manage the GPG and RSA signing keys used to sign packages for authentication and the RSA keys used to sign and verify the Alpine Linux Index files.
- Java Keystore: Manage the key store that holds the signing keys used to automatically sign JAR files downloaded from a virtual repository.
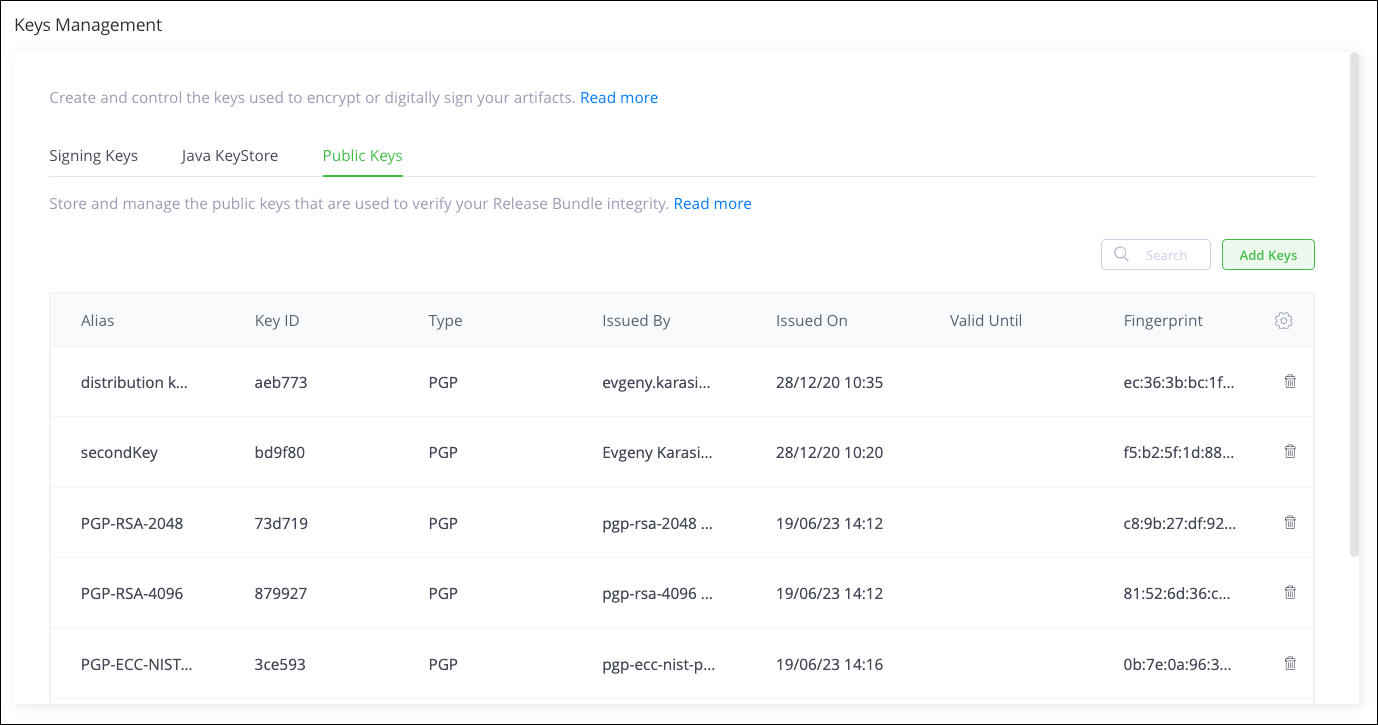
- Public Keys: Store and manage the public keys used to verify your Release Bundle integrity.
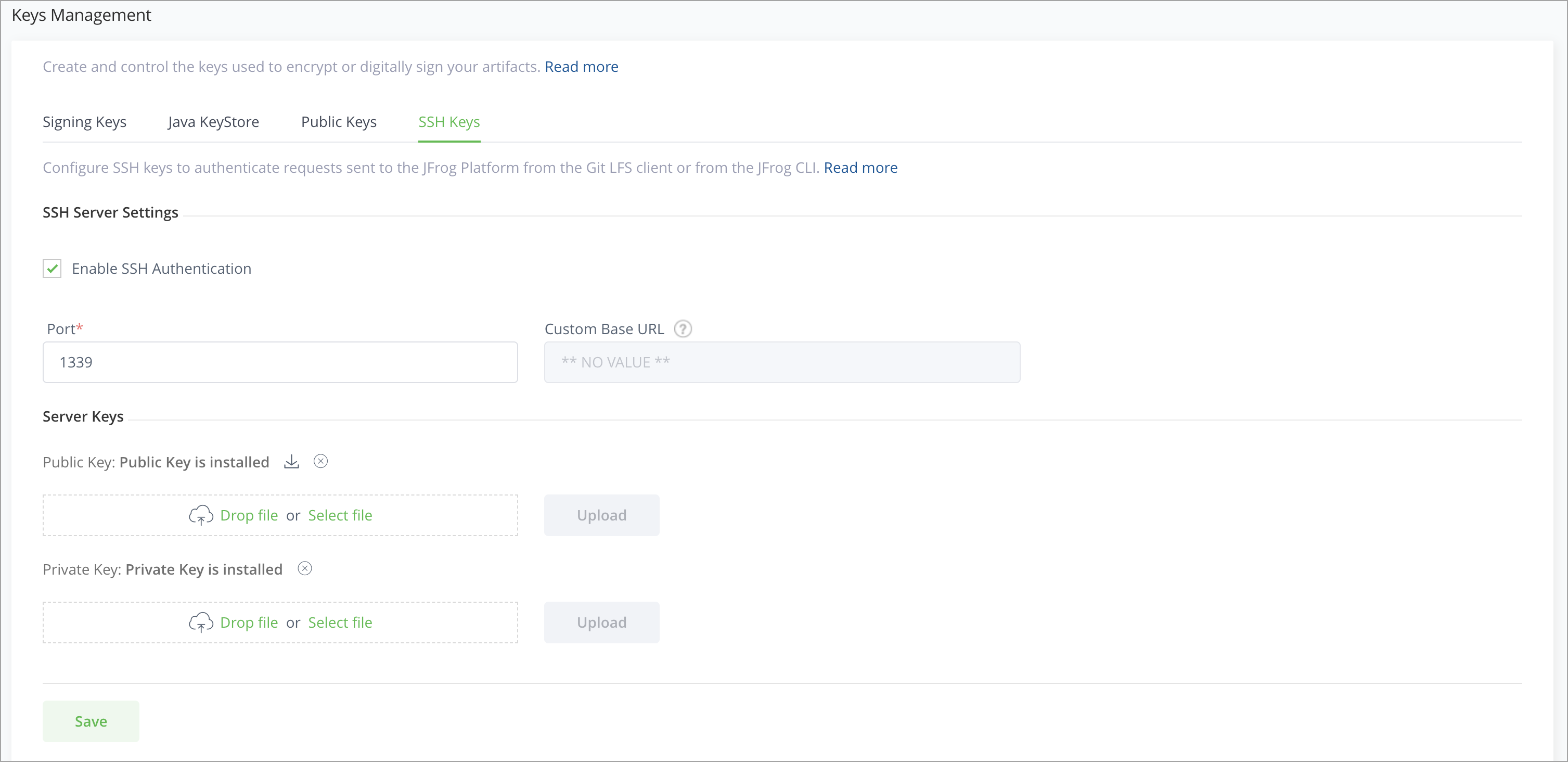
- SSH Keys: Configure SSH keys to authenticate requests sent to the JFrog Platform from a Git LFS client or from the JFrog CLI.
To access the Keys Management function, in the JFrog Platform UI, go to the Administration module and then go to Security > Keys Management. This displays the Keys Management window.
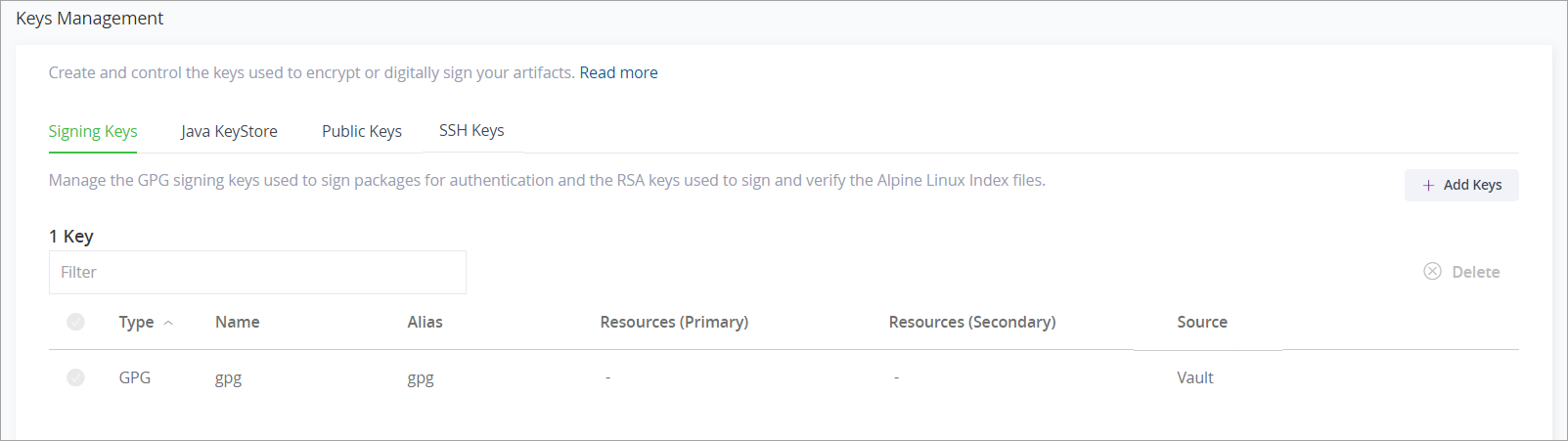
The centralized dashboard for creating and managing all signing keys displays the number of configured keys, the type, name, alias, primary resource, and secondary resource.
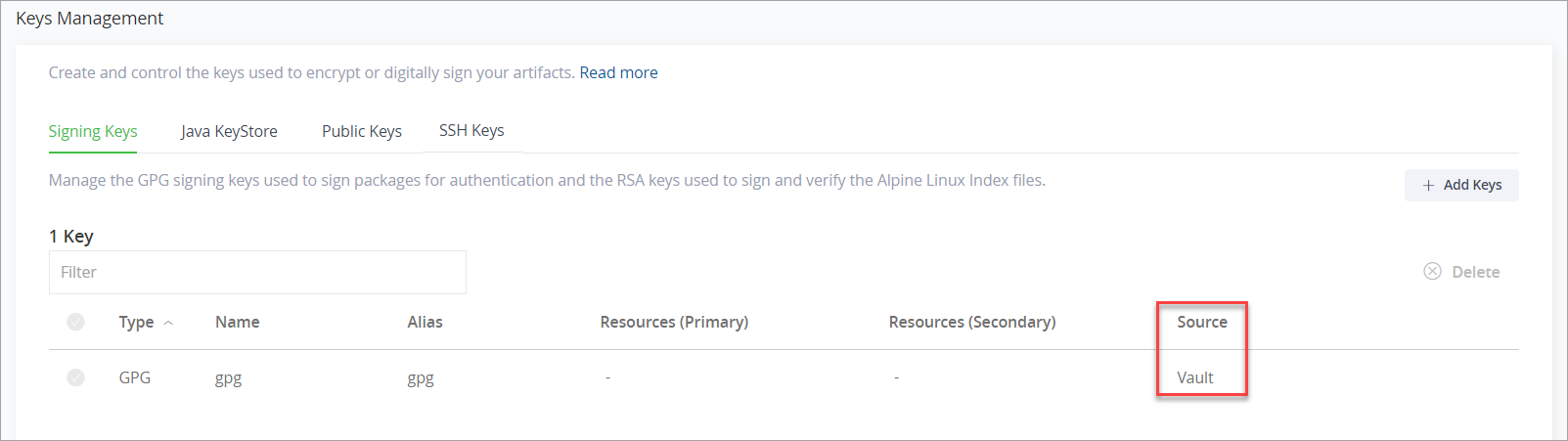
The Source column provides an indication of whether the key is an uploaded key or a Vault key:
- If there are multiple Vault connectors configured in your system, the Source will indicate which configured Vault connector is being used.
- If no connector is configured, the key's source will appear as "No connector is configured".
Next, follow the steps for creating and controlling the keys according to the type of key.
- Managing Signing Keys for RSA and GPG signing keys
- Managing WebStart and Jar Signing for the Java keystore
- Managing Public Keys
- Managing SSH Keys
Manage Signing Keys
RSA key pairs are used to sign and verify the Alpine Linux index files in JFrog Artifactory, while GPG key pairs are used to sign and validate package integrity. The JFrog Platform enables you to manage multiple RSA and GPG signing keys through the Keys Management UI and REST API. The JFrog Platform supports managing multiple pairs of GPG signing keys to sign packages for authentication of several package types such as Debian, Opkg, and RPM through the Keys Management UI and REST API.
Note
Artifactory signs repository metadata (not packages) for RPM, Debian, Opkg, and Alpine.
Manage RSA and GPG Key Pairs
In the JFrog Platform, you can upload, view or remove the RSA/GPG Keys in the Administration module, under Security | Keys Management.
Add RSA Keys Pairs
JFrog Platform lets you manage multiple pairs of RSA signing keys, so you can sign Alpine packages for authentication.
Generate RSA Keys
The way to generate keys is platform-dependent. For more information, see Build a Public and Private RSA Key.
Upload RSA Keys
-
In the JFrog Platform UI, go to the Administration module and then go to Artifactory | Security | Keys Management.
-
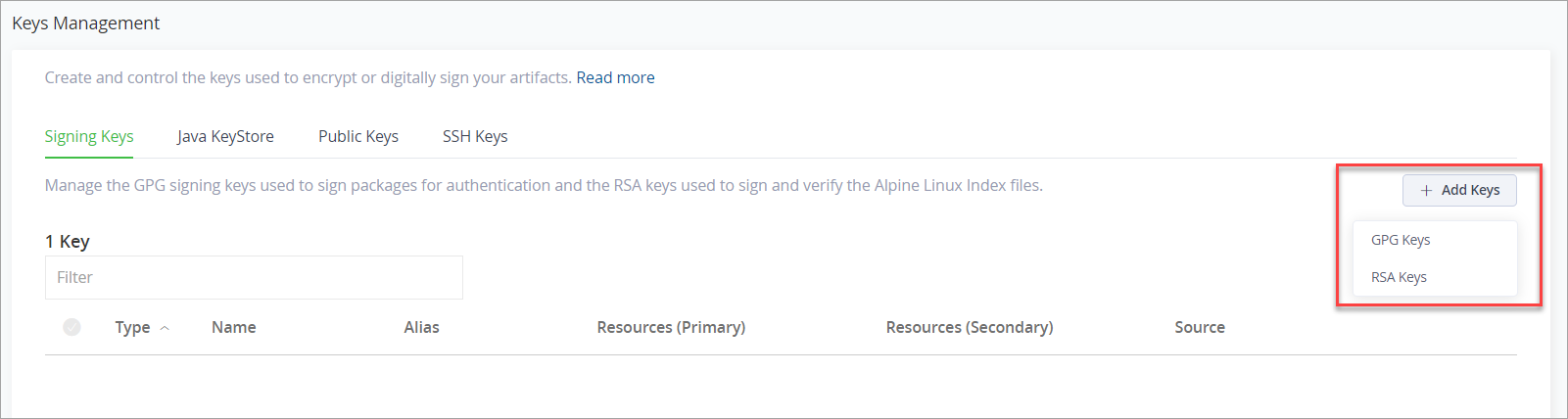
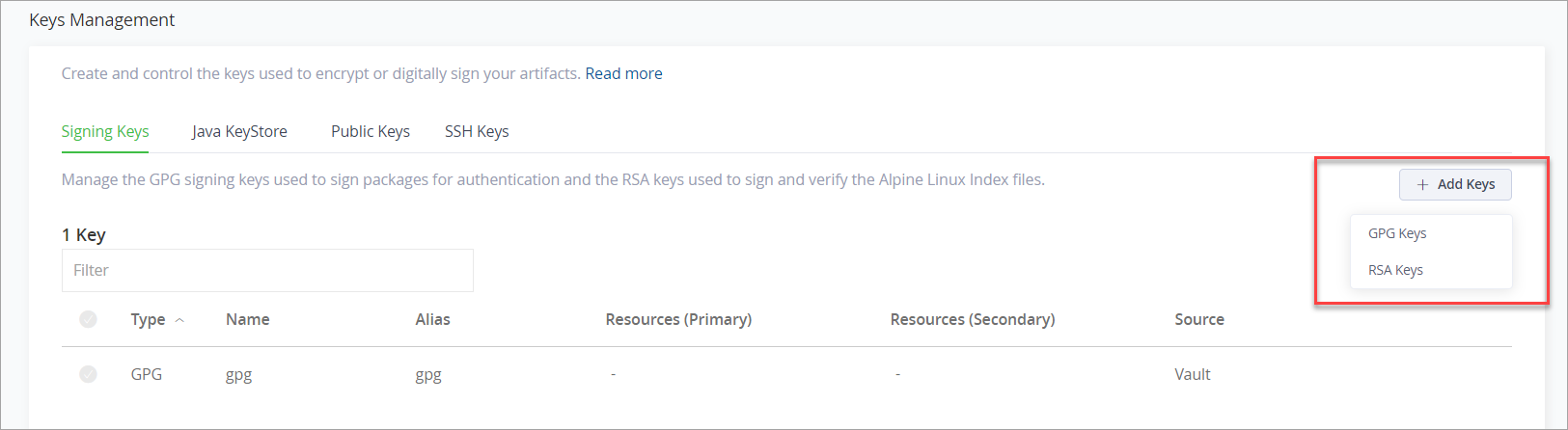
Click + Add Keys, and from the dropdown, select RSA Keys.
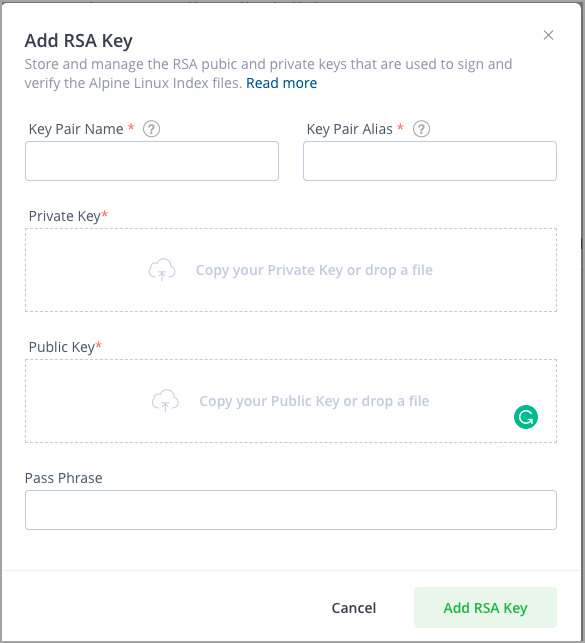
This opens the Add RSA Key window.
-
Enter the RSA parameters generated when creating the RSA Key Pair.
-
Click Add RSA Key to save the new key.
Configure Alpine Repositories with RSA Keys
Alpine Linux requires RSA keys by default.
To learn more about configuring keys for Alpine Linux packages, see Connect apk to Artifactory.
Add GPG Key Pairs
JFrog Platform lets you manage a pair of GPG signing keys so you can sign packages for authentication in several formats such as Debian, Opkg and YUM.
Generate GPG Keys
The method of generating keys is platform-dependent. The following example shows how to generate the public and private keys on Linux.
# generate the keys
gpg --gen-key
# list all keys in your system and select the pair you want to use in Artifactory
gpg --list-keys
# resolve the key-id from the lists-keys by selecting the relevant license
pub 2048R/8D463A47 2015-01-19
uid JonSmith (Jon) <[email protected]>
key-id = 8D463A47
#export the private key with the specified id to a file
gpg --output {private key file name and path} --armor --export-secret-keys {key-id}
#export the public key with the specified id to a file
gpg --output {public key file name and path} --armor --export {key-id}You also need to specify a passphrase to use with the signing keys. You can save the passphrase or pass it with a REST API call.
Upload GPG Keys
Use the procedure below to upload a GPG key pair (public and private keys) to Artifactory.
Note
The keys are generated outside of Artifactory. For more information, see Generate GPG Keys.
To upload a GPG key pair to Artifactory:
-
To upload your signing keys, go to the Administration module and then go to Artifactory | Security | Keys Management.
-
Click + Add Keys, and from the dropdown list, select GPG Keys.
This opens the Add GPG Key window.
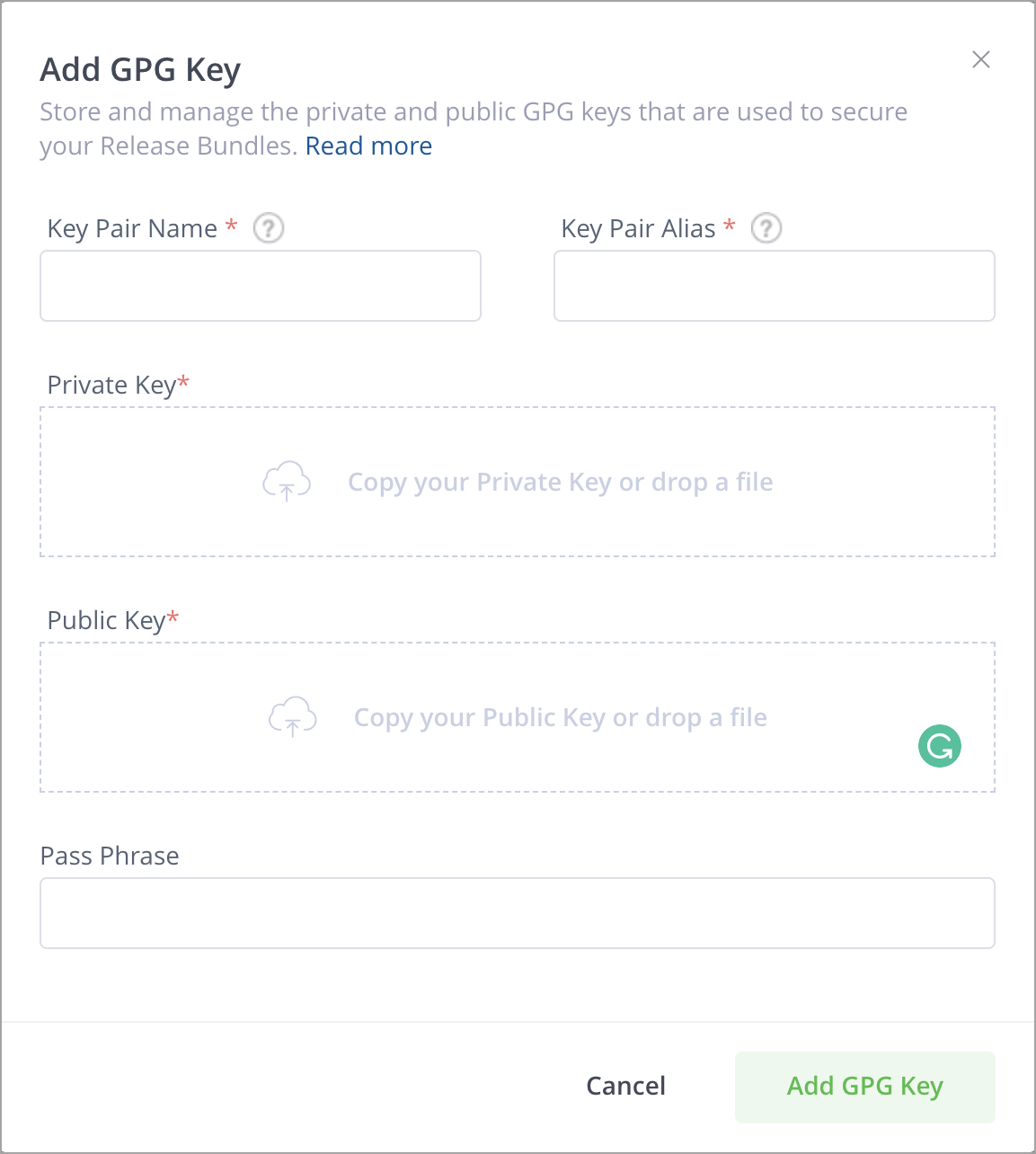
-
Enter the details for the GPG key pair.
-
Click Test to test the configuration.
-
If the test is successful, click Add GPG Key to save the new key pair.
-
Artifactory will indicate when the keys are installed, and you can click the Public key is installed link to download the public key.
After you have uploaded your new GPG keys, you can use them for JFrog Distribution. For more information, see JFrog Distribution GPG Signing.
When working with Release Bundles v2, you can use the keys to sign a Release Bundle version and then propagate those keys to Distribution (Enterprise+ users only). For more information, see Create Signing Keys for Release Bundles (v2).
Upload GPG Keys using the REST API
You can upload a GPG key pair to Artifactory using the Create Key Pair REST API.
Manage Vault RSA and GPG Key Pairs
In addition to uploading keys, you can also choose to store your signing keys in HashiCorp Vault as secrets, and retrieve them in the JFrog Platform. For more information on configuring and enabling HashiCorp Vault, see Vault Integration.
When Vault is enabled in your JFrog Platform, keys that have been stored in Vault will appear in the Source column under "Vault".
When Vault is enabled, you can either add new RSA/GPG keys and store them in Vault, or change the uploaded keys with Vault ones.
Set up a New RSA/GPG Key in Vault
-
Click +Add Keys and select GPG or RSA.
This opens the Add GPG (or RSA) Key window.
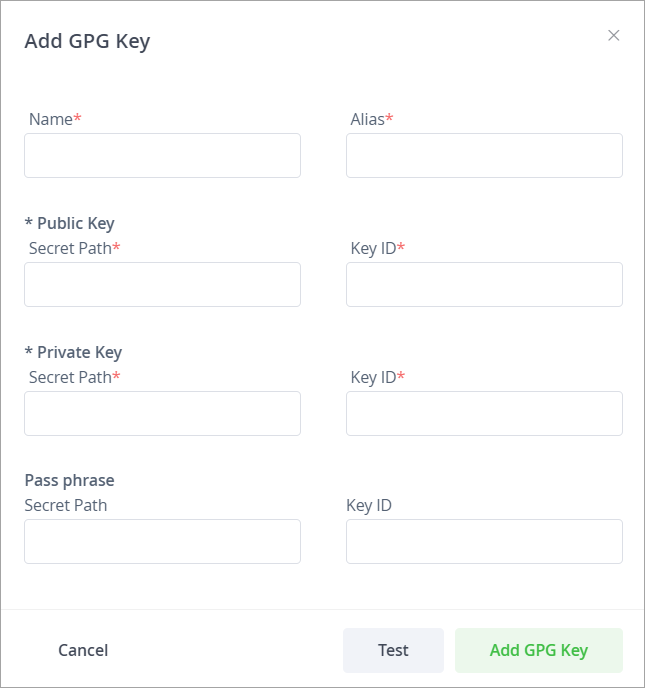
-
From the Vault Connector dropdown list, select the Vault connector you wish to use for the key.
-
Enter the details for the key.
-
Click Test to test the configuration.
-
If the test is successful, click Add GPG (RSA) Key to save the new key.
Change an Uploaded Key with a Vault Key
Important
Once you change an uploaded key to a Vault one, the uploaded key will be deleted; this action cannot be undone.
-
In the Signing Key list of keys, go to the arrow next to the uploaded key you wish to change to Vault and click it.
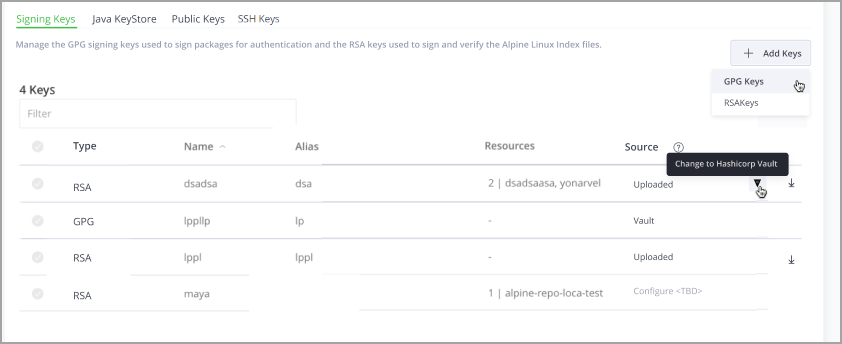
This opens the Change GPG/RSA Key to Vault window.
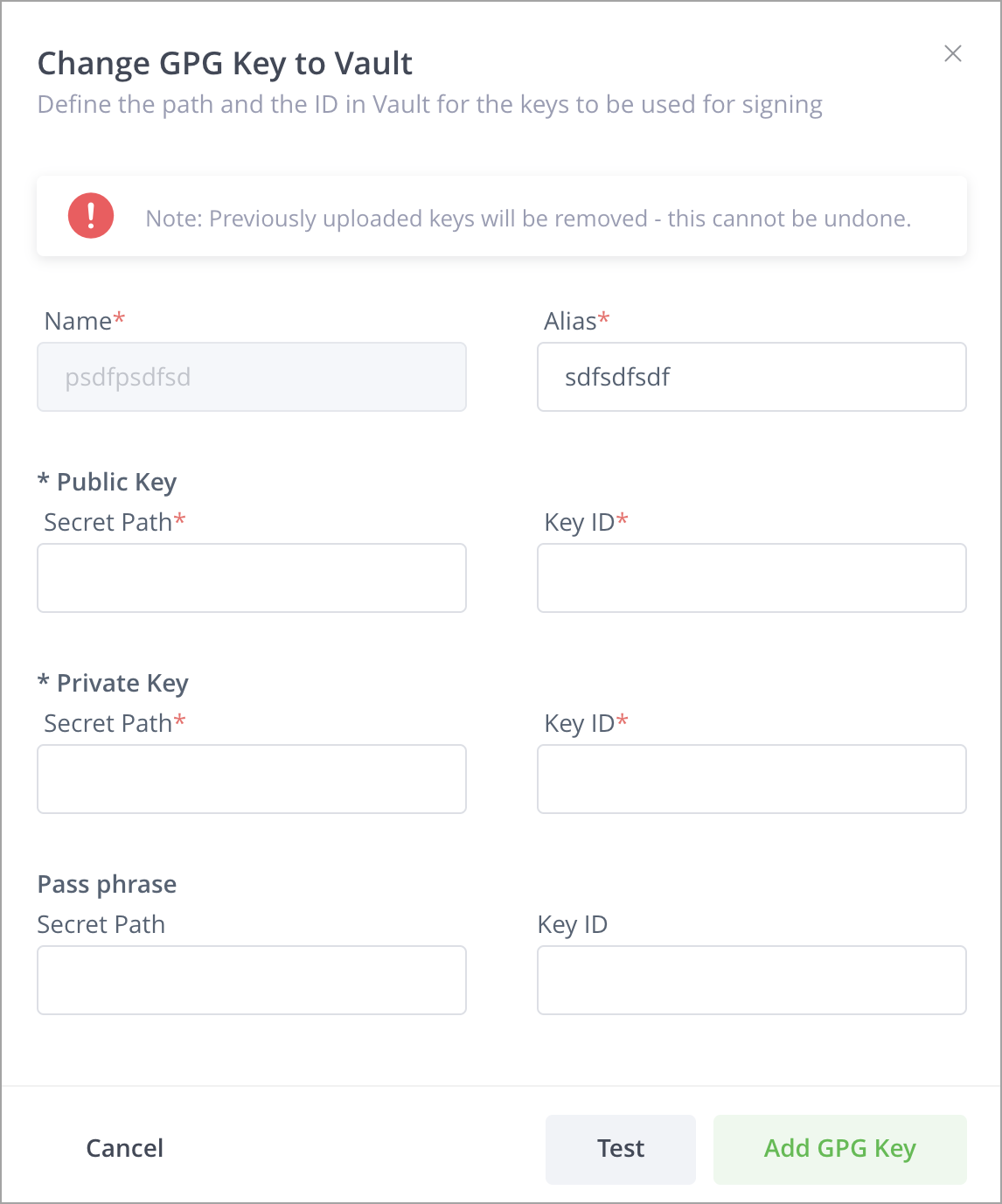
-
From the Vault Connector dropdown list, select the Vault connector you wish to use for the key.
-
Enter the details for the key.
-
Click Test to test the configuration.
-
If the test is successful, click Add GPG (RSA) Key to save the new key.
REST API Commands to Manage Keys
The JFrog Platform supports managing multiple pairs of GPG signing keys using a set of REST APIs. This feature enables you to assign a signing key pair per repository, providing you with the granularity to choose which keys to use to sign the artifacts in repositories instead of using the same key pair to sign all artifacts.
Manage WebStart and Jar Signing
Java Web Start is a technology developed by Sun Microsystems (now Oracle) to allow you to download and run Java applications directly from your browser with one-click activation.
Java Web Start requires that any JAR downloaded is signed by the software vendor. To support this requirement, Artifactory lets you manage a set of signing keys that are used to automatically sign JAR files downloaded from a virtual repository.
For more information, see the Oracle documentation for Java Web Start.
Signing keys are managed in the Administration module under Artifactory | Security | Keys Management.
Note
Artifactory signs repository metadata (not packages) for RPM, Debian, Opkg, and Alpine.
Generate JAR Signing Keys
To sign JAR files, you first need to create a keystore, and generate and add key pairs to it. These can be created with Oracle's keytool utility, that comes built into your Java Runtime Environment (JRE), by executing the following command:
keytool -keystore <keystore filename> -keypass <key_password> -storepass <store_password> -alias <store_alias> \
-genkeypair -dname "cn=<cName>, ou=<orgUnit>, o=<orgName>, S=<stateName>, c=<country>" -validity <days>For more information, refer to the Oracle keytool - Key and Certificate Management Tool documentation.
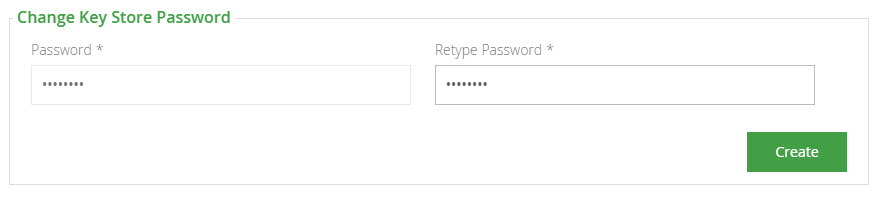
Set Your Keystore and JAR Signing Keys
Before you can add a keystore, you must set the password needed to make any later changes to the keystore. You will need this password to remove or update the keystore.
Set the password and click Create. This will unlock the rest of the keystore management fields.
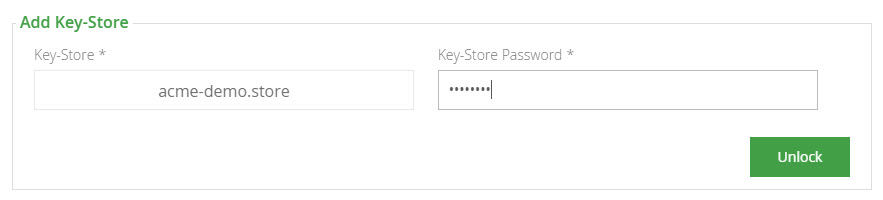
Once your keystore password is set and you have created a keystore and a set of signing keys, you can add them to Artifactory.
First upload your keystore file under Add Key-Store and enter the keystore password. Click Unlock.
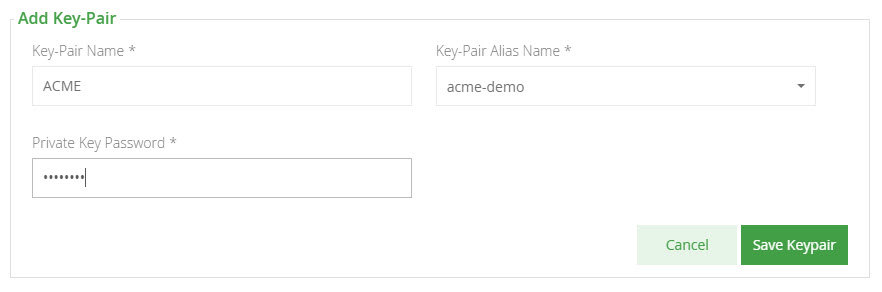
Once your keystore is set in Artifactory you may add key pairs under Add Key-Pair.
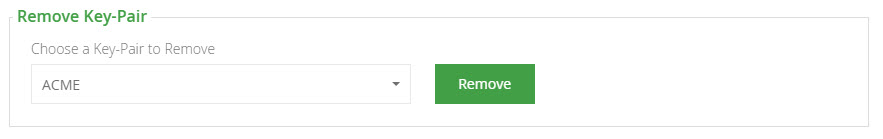
Remove a JAR Signing Key Pair
To remove a key pair, simply select the key pair and click "Remove".
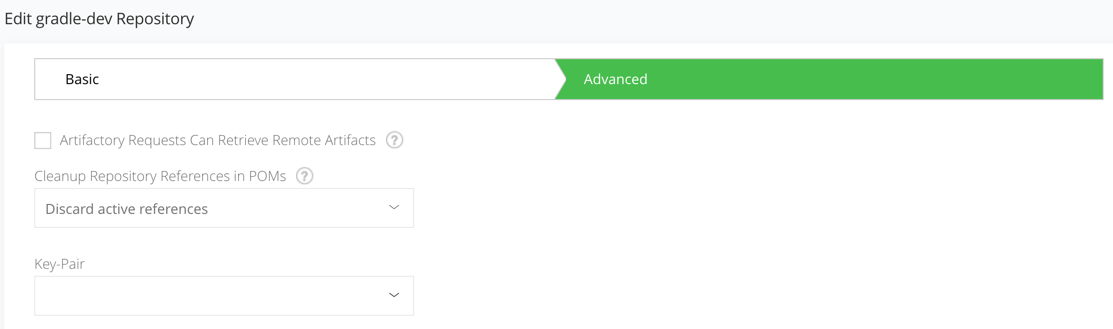
Configure Virtual Repositories to Sign JARs
Once Artifactory has a keystore and key pairs, you can configure a virtual repository with the key pair you wish to use for JAR signing. This is done in the Advanced settings of the virtual repository configuration screen.
Manage Public Keys
Subscription Information
This feature is supported with the Enterprise+ license.
To create trust between Distribution, source Artifactory instances, and Artifactory Edge nodes in the JFrog Platform, you will need to deploy the relevant public GPG key to each service.
Create your signing key using the following sections:
- Distribution service: Set Signing Key for Distribution REST API
- Source Artifactory and Artifactory Edge node: Set GPG Public Key REST API
For more information, see Managing Signing Keys.
Note
If Vault is configured, follow the steps in Vault.
You can upload your public GPG key to the source Artifactory instance and Artifactory Edge instances in the Administration module. Go to Administration > Security > Keys Management. and select the Public Keys tab.
Add a Public Key
-
Click Add Keys.
This opens the Add Public Key window.
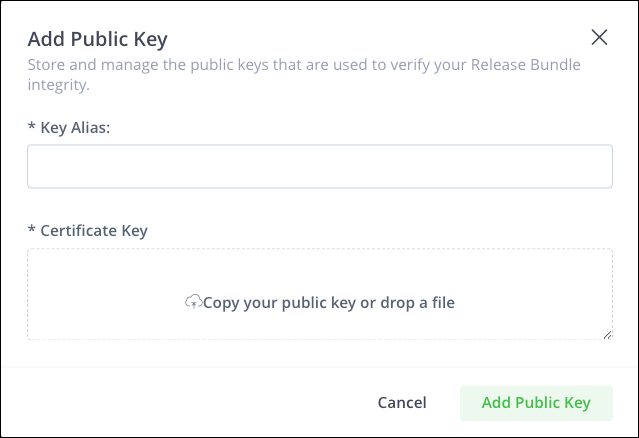
-
Enter the Key Alias and then copy your public key or drop a file into the Certificate Key field.
-
Click Add Public Key.
Manage SSH Keys
JFrog Artifactory supports SSH authentication for Git LFS and the JFrog CLI using RSA public and private keys. This allows these tools to exchange sensitive information with the Artifactory server that is authenticated via SSH. You will need to configure SSH keys to authenticate requests sent to the JFrog Platform from Git LFS client or from the JFrog CLI.
There are two main facets of SSH authentication:
Server authenticates itself to the client
The server must be authenticated before you send it any confidential data. For example, you should not authenticate a user to the server with the user's password before the server has been authenticated. The server is authenticated in the following manner:
When the SSH connection is established, the server sends its public key to the client, and the client matches the key to a list of known public keys stored in a known_hosts file (before the first ever connection to the server, you must obtain the server's public key by some other means and add it to the known_hosts file manually). This verifies that the server is indeed the owner of the stored public key, since only that server will have the corresponding private key. It also verifies that the server is known (and not an imposter) since its public key is stored in the known_hosts file.
User authenticates itself to the server
This process mirrors the process of the server being authenticated to the client. The user must first provide their public key to the server, which stores the key in the user's account authorization list. Then, when the user tries to log in, the server sends the user back their public key, and the user must show that they hold the corresponding private key.
Limitation
SSH is not supported on the Artifactory SaaS cloud service.
To configure SSH authentication, you will need to execute the following main steps:
Configure SSH Server Authentication
-
In this step, you will configure Artifactory's SSH authentication parameters. First, you need to generate an SSH key pair for Artifactory. For example, on a Linux-based system, you could execute the following command.
ssh-keygen -t rsa -C "[email protected]" -
Next, to configure Artifactory for SSH authentication, go to the Administration module, select Artifactory | Security | Keys Management and click the SSH Keys tab.
-
Fill in the details for the Server Settings and the Server Keys.
| Server Setting | Description |
|---|---|
| Enable SSH Authentication | When checked, SSH authentication is enabled. |
| Port | The port that should be used for an SSH connection. |
| Custom URL Base | The Custom Base URL that should be used for SSH connections. Note that this is the same Custom URL Base configured in the Administration module under Configuration | General. |
| Public key/ Private key | The key pair used for authentication. |
Configure User Authentication with your Public Key
In this step, you will configure Artifactory with your public key so that you may be authenticated when sending requests to Artifactory from the Git LFS client or from the Artifactory CLI.
First, you need to generate a key pair. For example, on a Linux-based system, you could execute the following command:
ssh-keygen -t rsa -C "[email protected]"Your public and private keys should be created under the ~/.ssh folder.
Don't forget to update your public key
Update your public key under the SSH section of your User Profile.
Configure the GIT LFS or CLI Client
To configure your Git LFS client, see Authenticating with SSH.
Control Your SSH Server Security
Controlling your SSH Server Security depends on your JFrog deployment:
- In a Cloud deployment, contact JFrog support, to make the required changes to your SSH Server Security.
- In a self-hosted deployment, you can control your SSH Server Security. Requires Platform Administrator permissions.
You can now control ciphers, MACs, signatures, and key exchange algorithms that are accepted by the Artifactory SSH server.
These values are left empty/null by default, and can have values delimited by comma (,) similarly to the correlating properties, and will be applied only if the corresponding artifactory.ssh.*.algorithms is not set.
Include Pattern System Properties for SSH Configuration
From Artifactory 7.18.6, the following constant values have been added as Include Only algorithms:
artifactory.ssh.cipher.algorithms=artifactory.ssh.key.exchange.algorithms=artifactory.ssh.mac.algorithms=artifactory.ssh.signature.algorithms=
Exclude Pattern System Properties for SSH Configuration
The Exclude patterns are:
artifactory.key.exchange.black.list=...artifactory.cipher.black.list=...
From Artifactory 7.18.6, the additional system properties were added to the exclude patterns.
artifactory.ssh.mac.black.list=...artifactory.ssh.signature.black.list=...
Supported Values By Algorithm Type for SSH Configuration
Note
Deprecated values are not loaded by default.
Algorithm Type | Values (loaded by default) | Deprecated (not loaded unless configured by name) |
|---|---|---|
Cipher Algorithms |
|
|
Key Exchange Algorithms |
|
|
Message Authentication Codes (MAC) Algorithms |
|
|
Signature Algorithms |
|
|
Updated 6 days ago

